Summary Points
-
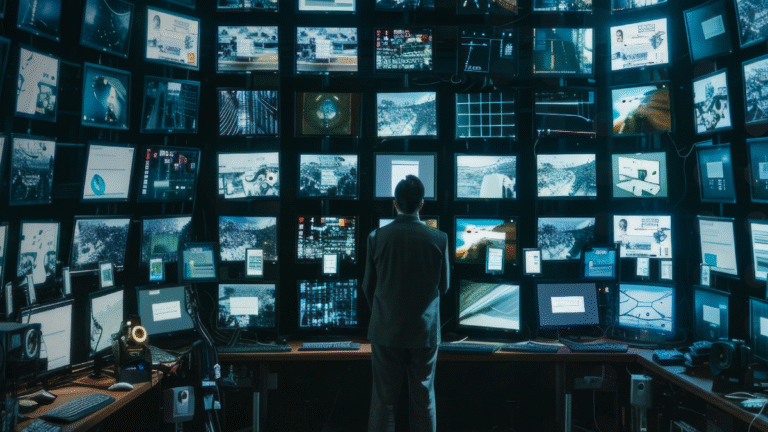
Exposed Cameras: Over 40,000 security cameras globally, notably 14,000 in the US, are accessible via the internet, posing severe cybersecurity risks.
-
Types and Vulnerabilities: HTTP and RTSP cameras can unintentionally expose live feeds or their administrative interfaces, making them targets for cyberattacks, espionage, and stalking.
-
Prevalent Industries: The telecommunications sector accounts for 79% of these exposed cameras, followed by technology (28.4%) and media/entertainment (19.6%), with significant risks across multiple sectors.
- Protection Measures: Users are advised to secure connections, change default credentials, disable unnecessary remote access, keep devices updated, and monitor for unusual logins to safeguard their privacy.
Problem Explained
A recent alert from cybersecurity firm Bitsight has unveiled a staggering security lapse affecting over 40,000 surveillance cameras worldwide, primarily due to their exposure on the internet through HTTP and Real-Time Streaming Protocol (RTSP). This vulnerability allows unauthorized individuals to access live feeds by merely knowing the camera’s IP address, turning these devices into potential tools for cyberattacks, extortion, and even stalking. The majority of the compromised cameras are located in the United States, with California and Texas leading the count. The telecommunications sector bears the brunt of this exposure, accounting for 79% of the affected cameras, largely due to the use of consumer-grade devices connected to residential networks.
Bitsight highlights an alarming trend: threat actors are actively scanning for these exposed cameras, utilizing dark web forums to share methods for exploitation. Although the existence of unprotected cameras might not seem immediately perilous, they can serve as gateways for broader cyber intrusions into organizational networks. In response to this pervasive threat, Bitsight urges users to adopt stringent security measures, such as updating device firmware and disabling unnecessary remote access, to safeguard their privacy and prevent their footage from becoming publicly accessible.
Critical Concerns
The exposure of over 40,000 security cameras worldwide, particularly those in sensitive sectors like telecommunications, raises severe risks not only for individual users but also for businesses and organizations that rely on robust cybersecurity frameworks. When these cameras, often inexplicably connected to the internet with inadequate protection measures, become accessible, they inadvertently serve as conduits for cybercriminal activities, including espionage and data exfiltration. For instance, if a malicious actor exploits these vulnerabilities to gain access to a company’s network via an exposed camera within an office, it could lead to extensive data breaches, breaches of customer trust, and financial losses. The interconnected nature of technology means that no organization operates in isolation; a breach in one can catalyze a domino effect, jeopardizing others in a supply chain or industry ecosystem. Therefore, the ramifications of such security lapses extend beyond individual accountability, highlighting the imperative for collective vigilance and proactive security measures to safeguard the integrity of interconnected networks.
Possible Remediation Steps
The recent exposure of 40,000 security cameras to remote hacking underscores the critical necessity for prompt remediation efforts in preserving both security and privacy.
Mitigation Steps
- Firmware Updates
- Network Segmentation
- Access Controls
- Intrusion Detection Systems
- User Authentication Enhancements
- Security Audits
NIST CSF Guidance
According to the NIST Cybersecurity Framework (CSF), organizations should adopt a proactive stance on risk management, focusing on identifying, protecting, detecting, responding to, and recovering from incidents. For deeper insights, refer to NIST Special Publication 800-53, which provides comprehensive security and privacy controls tailored for information systems.
Stay Ahead in Cybersecurity
Stay informed on the latest Threat Intelligence and Cyberattacks.
Learn more about global cybersecurity standards through the NIST Cybersecurity Framework.
Disclaimer: The information provided may not always be accurate or up to date. Please do your own research, as the cybersecurity landscape evolves rapidly. Intended for secondary references purposes only.
Cyberattacks-V1