Essential Insights
-
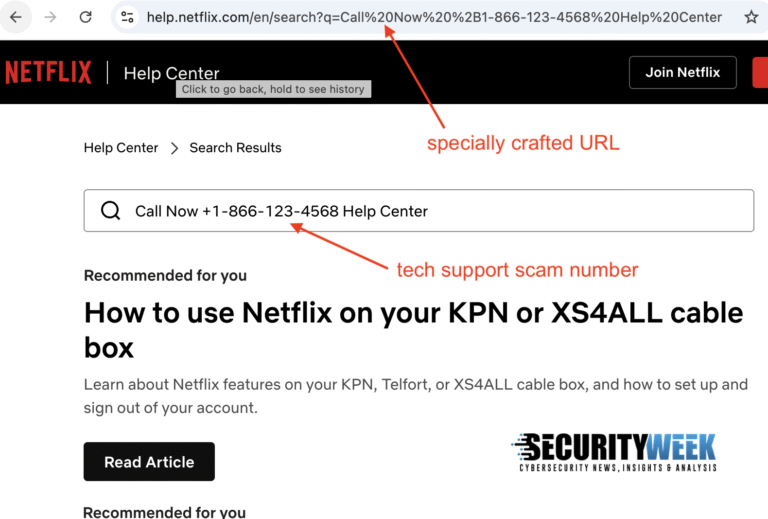
Exploiting Legitimate Websites: Tech support scammers are ‘hacking’ major company websites to display their phone numbers, tricking users into calling them for support.
-
Misleading Sponsored Ads: Scammers are buying Google ads that direct users to genuine sites like Apple and Microsoft, but the URLs are manipulated to show scam phone numbers in search results.
-
Search Parameter Injection: This method uses search parameter injection techniques to poison search results on real support pages, making the fraudulent number appear legitimate.
- Endangering Personal Data: Once contacted, scammers impersonate the brand to steal personal information, financial data, or gain remote access to victims’ computers.
Problem Explained
Tech support scammers have devised an insidious yet simplistic strategy to ensnare unsuspecting users by exploiting the websites of reputable companies. According to an analysis by the cybersecurity firm Malwarebytes, these unscrupulous actors purchase sponsored ads on Google that lead users searching for technical assistance directly to the legitimate help pages of well-known corporations like Apple, Microsoft, and PayPal. However, these pages contain cleverly manipulated URLs that trigger “search parameter injection,” causing the scammers’ phone numbers to appear deceptively within the official site’s search results, thus bypassing the need for fake websites.
The manipulation is so subtle that users may not initially recognize the dissonance, as the browser’s address bar still displays the legitimate company’s URL, thereby fostering a false sense of security. Once individuals call the fraudulent number, scammers exploit this trust by impersonating the company to extract sensitive personal and financial information. Jerome Segura, Malwarebytes’ Senior Director of Research, emphasizes the gravity of the situation, especially regarding financial entities like Bank of America and PayPal, where the ultimate aim is to siphon funds from unsuspecting victims. This alarming trend not only highlights the creativity of cybercriminals but also underscores the pervasive vulnerability of users navigating digital landscapes in search of assistance.
Critical Concerns
The emergence of tech support scammers exploiting major company websites poses significant risks not only to unsuspecting users but also to the broader business landscape. When esteemed brands like Apple and Microsoft are hijacked to display fraudulent contact information, it undermines customer trust and brand integrity, leading to decreased user engagement and potential financial losses. Users, misled into divulging personal or financial information, can face dire consequences, including identity theft and monetary fraud, amplifying the fallout for the legitimate companies that inadvertently facilitated this deception. Consequently, organizations may encounter heightened reputational damage, increased customer service burdens, and regulatory scrutiny, culminating in a pervasive atmosphere of skepticism that adversely affects consumer confidence across the industry. The ripple effects of such scams extend well beyond individual incidents, potentially destabilizing relationships between consumers and other businesses that rely on trust and transparency in a digital marketplace.
Possible Remediation Steps
Timely remediation is essential in mitigating the repercussions of high-profile tech support scams that exploit well-known platforms like Apple, Netflix, and Microsoft. Prompt action can prevent further damage and protect both users and corporate reputations.
Mitigation and Remediation Steps
- Incident Response Plan: Activate designated protocols for immediate action.
- User Awareness: Educate users on recognizing phishing attempts and fraudulent activity.
- System Updates: Ensure software and security systems are up-to-date to close vulnerabilities.
- Access Controls: Limit system access according to the principle of least privilege.
- Threat Intelligence: Monitor and analyze threat landscapes to anticipate future scams.
- Communication Strategy: Inform stakeholders and clients clearly and promptly about the breach and recovery efforts.
- Regular Audits: Conduct audits to identify security gaps and enhance defense mechanisms.
NIST CSF Guidance
The National Institute of Standards and Technology’s Cybersecurity Framework (CSF) emphasizes a proactive approach to risk management, prioritizing detection, response, and recovery strategies. For deeper insights into effective controls and frameworks, refer specifically to NIST Special Publication 800-53.
Advance Your Cyber Knowledge
Explore career growth and education via Careers & Learning, or dive into Compliance essentials.
Explore engineering-led approaches to digital security at IEEE Cybersecurity.
Disclaimer: The information provided may not always be accurate or up to date. Please do your own research, as the cybersecurity landscape evolves rapidly. Intended for secondary references purposes only.
Cyberattacks-V1