Summary Points
-
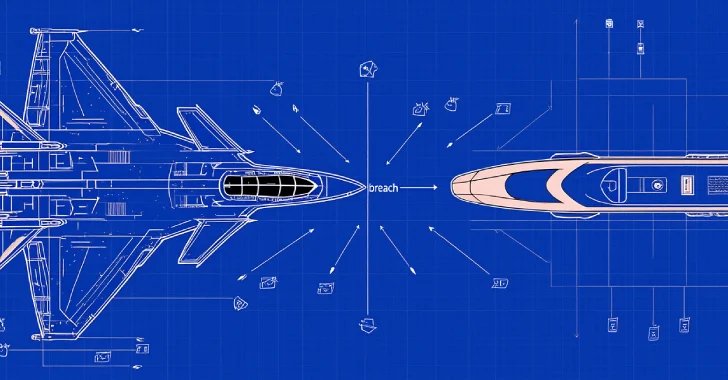
Targeted Cyber Espionage: TAG-140, linked to a hacking group associated with Pakistan, is actively targeting Indian governmental sectors using a modified remote access trojan (RAT) called DRAT V2, leveraging sophisticated phishing techniques to compromise institutions.
-
Advanced Malware Tactics: DRAT V2 features improved command execution capabilities and obfuscation techniques, facilitating persistent control over infected systems while complicating detection and monitoring efforts, though it lacks advanced anti-analysis measures.
-
Evolving Threat Landscape: The group’s focus has expanded to include various ministries beyond defense, showcasing an adaptive malware arsenal that evolves to obscure signatures and enhance operational flexibility, heightening the stakes for cybersecurity in India.
- Persistent Cyber Threats: Other groups, including APT36 and Confucius, are also executing sophisticated phishing campaigns and deploying advanced malware, underscoring the ongoing and multifaceted nature of cyber threats aimed at India’s national security.
Key Challenge
A newly identified hacking group with connections outside of Pakistan, designated as TAG-140, has been targeting Indian government organizations using a modified version of a remote access trojan (RAT) called DRAT V2. This activity, documented by Recorded Future’s Insikt Group, is believed to be associated with SideCopy, a sub-collective beneath the Transparent Tribe umbrella. The group’s modus operandi has evolved to include sophisticated social engineering tactics, notably spoofing the Indian Ministry of Defence through a counterfeit press release portal. This has enabled them to deliver malware that enhances their reconnaissance and data exfiltration capabilities while complicating detection and attribution efforts.
The scope of TAG-140’s attacks has expanded beyond traditional sectors, now encompassing railway, oil and gas, and external affairs ministries, evidencing a calculated shift in target selection. Reported by Recorded Future, this latest campaign underscores the adversary’s iterative improvements in malware architecture and command functions, thereby solidifying their potential for persistent infiltration and control over compromised systems. This pattern of cyber aggressions illustrates a broader trend of escalating cyber threats against India, driven by increasingly sophisticated tactics from groups like APT36, underscoring a significant concern for national security.
What’s at Stake?
The ongoing cyber incursions led by the TAG-140 group, with their innovative use of the DRAT V2 malware, present a significant risk not only to targeted Indian government entities but also to a diverse array of businesses and organizations across multiple sectors—ranging from defense to energy. If these malicious activities were to propagate beyond their initial focus, the prospects for widespread disruption and data breaches become alarmingly tangible. Affected organizations may face severe operational setbacks due to potential data exfiltration, service disruptions, and compromised sensitive information, leading to financial losses, reputational damage, and legal ramifications. Furthermore, the ripple effects of such breaches could undermine user trust and safety, prompting even broader vulnerabilities within supply chains and collaborative networks. Consequently, vigilance, adaptive cybersecurity measures, and timely threat intelligence sharing are imperative to mitigate the repercussions of this evolving threat landscape.
Fix & Mitigation
The urgency of immediate intervention in cybersecurity incidents cannot be overstated, particularly when they involve sophisticated threats such as the TAG-140 group deploying DRAT V2 RAT against critical sectors like government, defense, and railways.
Mitigation Steps
-
Incident Detection
- Implement advanced threat detection systems.
- Utilize anomaly detection tools.
-
Containment Strategies
- Isolate affected systems.
- Restrict network access.
-
Eradication of Threats
- Remove malware and suspect files.
- Patch vulnerabilities.
-
Recovery Measures
- Restore systems from clean backups.
- Verify system integrity before bringing online.
-
Ongoing Monitoring
- Establish continuous monitoring protocols.
- Conduct regular security audits.
- Employee Training
- Provide training on recognizing phishing attempts.
- Promote a culture of cybersecurity awareness.
NIST CSF Guidance
The NIST Cybersecurity Framework (CSF) underscores the criticality of timely risk response. Specifically, the framework emphasizes the necessity for organizations to identify, protect, detect, respond to, and recover from cybersecurity incidents effectively. For comprehensive strategies, refer to NIST Special Publication (SP) 800-53, which outlines security and privacy controls for federal information systems.
Advance Your Cyber Knowledge
Explore career growth and education via Careers & Learning, or dive into Compliance essentials.
Explore engineering-led approaches to digital security at IEEE Cybersecurity.
Disclaimer: The information provided may not always be accurate or up to date. Please do your own research, as the cybersecurity landscape evolves rapidly. Intended for secondary references purposes only.
Cyberattacks-V1