Summary Points
- North Korean threat actors, specifically the Jasper Sleet group, have infiltrated Western organizations via fraudulent employment schemes targeting Web3, blockchain, and crypto firms, bypassing traditional cyberattack methods.
- Two major leaks in August 2025 revealed 1,417 compromised email addresses, operational documents, and communication strategies, exposing systematic identity fabrication and social engineering tactics.
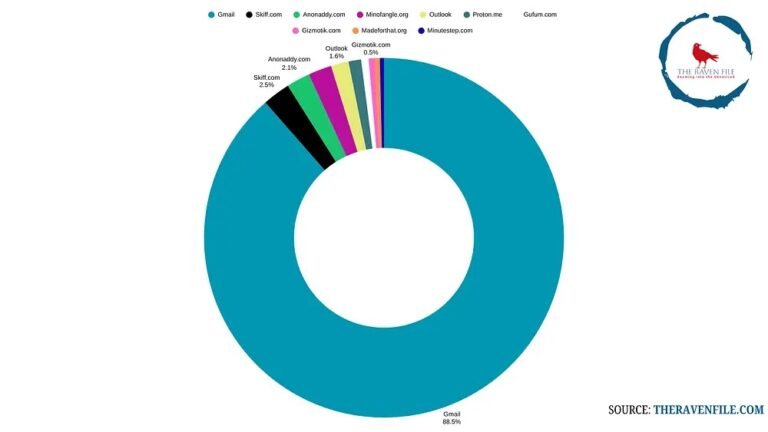
- The actors utilize consistent email naming patterns, temporary and compromised email providers, and culturally influenced identity cues to create convincing fake personas, often using shared passwords and password patterns like “123qwe!@#QWE.”
- They employ sophisticated privacy and obfuscation tools, such as Octo Browser and FaceSwap, necessitating organizations to enhance screening, including deepfake detection and rigorous background checks, to prevent infiltration.
Problem Explained
Recent cybersecurity intelligence has uncovered a highly sophisticated infiltration campaign led by North Korean state-sponsored hackers, specifically the Jasper Sleet group, which has targeted Western organizations involved in Web3, blockchain, and cryptocurrency sectors. Rather than relying on traditional hacking methods, these threat actors use fraudulent employment schemes, securing legitimate access by fabricating identities and manipulating social engineering tactics. Two significant data leaks in August 2025 have provided detailed insights into their operational strategies, revealing nearly 1,400 email addresses—and an additional 28—used for overseas employment, along with internal documents like expense sheets and communications. These leaks expose the scale and complexity of the operation, highlighting systematic identity creation, the use of privacy and temporary email platforms, and intricate patterns in naming conventions and password practices that serve to deceive security measures. The threat actors also employ advanced technological tools, such as fake video face swaps and proxy networks, which make detection more challenging. Organizations are urged to strengthen their screening and cybersecurity protocols, including deepfake detection and thorough background checks, to mitigate the risk of infiltration by such well-coordinated and clandestine covert operations.
The reports are produced by cybersecurity analysts at The Raven File, who have meticulously uncovered and analyzed these leaks, exposing the patterns, infrastructure, and techniques used by the North Korean hackers. The findings underscore the threat posed not just by the hackers’ technical skills but also by their disciplined operational security practices, which include systematic password protocols, curated persona construction, and technological obfuscation. This intelligence emphasizes the importance of proactive defense strategies to prevent infiltration, especially in high-value sectors like blockchain and cryptocurrencies, where the consequences of successful cyber-espionage can be severe and far-reaching.
Risk Summary
Recent cybersecurity intelligence uncovers a highly sophisticated infiltration campaign by North Korean state-sponsored hackers, specifically the Jasper Sleet group, targeting Western organizations—particularly in Web3, blockchain, and cryptocurrency sectors—through fraudulent employment schemes that bypass traditional exploits by gaining legitimate access. Leaked data from mid-2025 reveals the scale and complexity of these operations: nearly 1,400 email addresses connected to North Korean operatives, along with operational documents, expense sheets, and internal communications, exposing meticulous identity fabrication, strategic use of temporary and privacy-focused email platforms, and cultural patterns in identity creation, such as specific naming conventions and age targeting. These hackers employ social engineering and technological deception tools, including deepfake video technologies and proxy networks, to obscure their activities, making detection and prevention increasingly challenging. The breaches highlight vulnerabilities in conventional recruitment screening, emphasizing the need for advanced verification protocols, deepfake detection, and scrutiny of communication patterns to mitigate infiltrations that threaten organizational security, financial integrity, and national security.
Possible Next Steps
Addressing the uncovering of DPRK IT workers’ email addresses and hiring patterns promptly is crucial. Timely remediation minimizes risks associated with espionage, cyberattacks, and international security threats, thereby protecting organizational assets and national interests.
Mitigation Strategies
-
Enhanced Monitoring: Implement real-time surveillance of network activity related to identified email domains and IP addresses to detect suspicious behavior early.
-
Access Controls: Restrict and verify access to sensitive systems, ensuring only authorized personnel can reach critical information.
-
Employee Training: Educate staff on recognizing phishing attempts and suspicious communications linked to DPRK hacking efforts.
-
Threat Intelligence Integration: Incorporate up-to-date intelligence on DPRK cyber activities to inform security protocols and response plans.
-
Communication Protocols: Establish clear channels for reporting potential security breaches or anomalies as soon as they are detected.
-
Collaboration with Authorities: Work with cybersecurity agencies and law enforcement to coordinate efforts and share intelligence on DPRK activities.
-
Vulnerability Patching: Regularly update and patch all software and hardware to close security gaps exploited by threat actors.
- Incident Response Plan: Develop and rehearse a comprehensive response plan tailored to cyber espionage incidents involving state-sponsored actors.
Explore More Security Insights
Discover cutting-edge developments in Emerging Tech and industry Insights.
Learn more about global cybersecurity standards through the NIST Cybersecurity Framework.
Disclaimer: The information provided may not always be accurate or up to date. Please do your own research, as the cybersecurity landscape evolves rapidly. Intended for secondary references purposes only.
Cyberattacks-V1