Summary Points
- Cybercriminals are exploiting trusted AI platforms like Simplified AI for sophisticated phishing attacks aimed at stealing credentials, bypassing traditional security measures.
- The 2025 campaign involved impersonation emails, password-protected PDFs, and fake Microsoft 365 login portals, leveraging social engineering and technical evasion tactics.
- The use of reputable AI platforms complicates detection, as threat actors capitalize on widespread enterprise trust and AI tool adoption without sufficient security oversight.
- Security experts recommend implementing multi-factor authentication, employee training, monitoring AI platform use, and advanced threat detection to mitigate such AI-based cyber threats.
Problem Explained
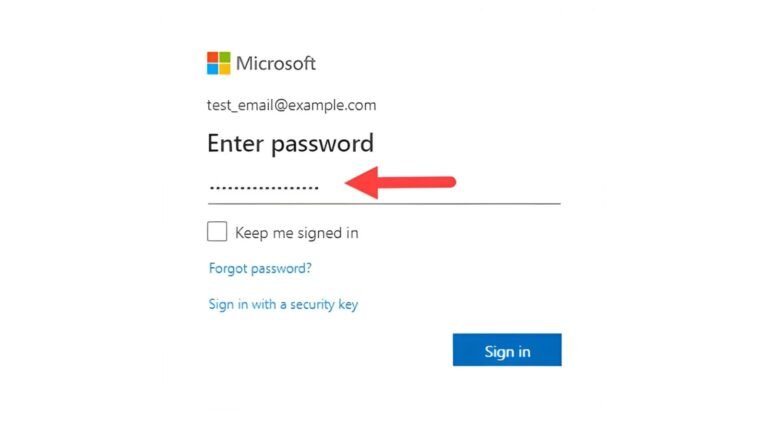
According to a recent report by cybersecurity firm Cato Networks, cybercriminals are increasingly exploiting trusted artificial intelligence (AI) platforms to conduct complex phishing attacks, targeting organizations by disguising malicious activity within familiar and legitimate tools. In July 2025, threat actors launched a sophisticated campaign using the popular marketing platform Simplified AI to steal Microsoft 365 credentials from US-based organizations, notably compromising at least one US investment firm. The attackers employed a multi-step strategy involving convincing emails impersonating pharmaceutical executives, password-protected PDFs containing malicious links, and redirection to fake yet realistic login pages designed to harvest enterprise credentials. This attack underscores a troubling shift in cybercriminal tactics, exploiting the widespread adoption of AI tools within corporate environments, which often lack robust security oversight.
The incident highlights a significant vulnerability: the reliance of organizations on reputable AI platforms, which criminals now manipulate to bypass traditional defenses. While many IT departments whitelist these sites to foster innovation, such trust can backfire, creating avenues for cybercriminals to infiltrate systems. Security experts warn that this evolving threat demands organizations implement stronger safeguards, including multi-factor authentication, vigilant monitoring of AI platform activity—even on unauthorized applications—and ongoing inspection of AI-related traffic. This breach serves as a critical reminder for entities to reassess their cybersecurity strategies—recognizing that even trusted platforms can become Trojan horses in an increasingly AI-driven digital landscape.
Risk Summary
Cybercriminals are increasingly exploiting trusted artificial intelligence (AI) platforms to carry out sophisticated phishing attacks, aiming to bypass traditional security defenses by leveraging the reputation of familiar tools already integrated into organizational workflows. A recent incident uncovered by Cato Networks involved threat actors using Simplified AI, a popular marketing platform, to steal Microsoft 365 credentials from a US investment firm through cleverly crafted emails impersonating corporate executives, embedding password-protected PDFs, and redirecting victims to fake, yet convincing, login portals. This method highlights a dangerous shift in cybercrime tactics where attackers rely on legitimate AI services, making detection more difficult and elevating the risk of data breaches across industries. The attack underscores the urgent need for organizations to implement multi-factor authentication, monitor AI platform activity—including shadow AI—and reinforce employee training to recognize social engineering schemes. As AI platforms become pervasive, firms must reevaluate their security strategies to address the emerging threats posed by the weaponization of trusted AI tools, balancing innovation with vigilance to prevent exploitation.
Possible Remediation Steps
In the rapidly evolving landscape of cybersecurity, swift and effective remediation is critical to prevent significant data breaches and protect organizational integrity, especially when hackers leverage AI to craft sophisticated phishing campaigns targeting Microsoft 365 credentials.
Detection
Implement advanced email filtering tools capable of identifying AI-generated phishing attempts. Regularly monitor system logs and user reports for suspicious activity.
User Training
Educate employees on recognizing AI-driven phishing emails, emphasizing caution with unexpected attachments or links and verifying sender identities.
Incident Response
Establish a clear, predefined incident response plan. Immediately isolate any suspected compromised accounts to prevent further abuse.
Credential Reset
Promptly reset passwords for compromised or potentially compromised Microsoft 365 accounts. Enforce multi-factor authentication to bolster security.
Security Patches
Ensure all software, especially email and security systems, are up to date with the latest patches to fix vulnerabilities exploited by attackers.
Threat Intelligence
Leverage threat intelligence services to stay informed about ongoing AI-based phishing tactics and adapt defenses accordingly.
Policy Updates
Review and strengthen email and security policies, including robust access controls and least privilege principles.
Third-party Collaboration
Coordinate with cybersecurity experts and Microsoft support for advanced detection tools and remediation strategies.
Continue Your Cyber Journey
Explore career growth and education via Careers & Learning, or dive into Compliance essentials.
Understand foundational security frameworks via NIST CSF on Wikipedia.
Disclaimer: The information provided may not always be accurate or up to date. Please do your own research, as the cybersecurity landscape evolves rapidly. Intended for secondary references purposes only.
Cyberattacks-V1