Top Highlights
-
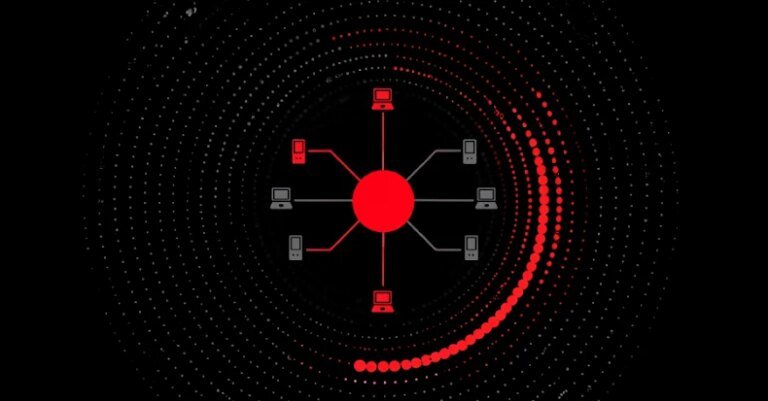
Expanded Targeting: The RondoDox botnet campaign exploits over 50 vulnerabilities across 30 vendors, targeting internet-exposed devices like routers and DVRs using a broad "exploit shotgun" approach.
-
Loader-as-a-Service Model: RondoDox has evolved its distribution method by using a ‘loader-as-a-service’ system, co-packaging its malware with Mirai and Morte payloads, enhancing detection challenges.
-
Significant Threat Landscape: Nearly 60 vulnerabilities are part of RondoDox’s arsenal, with 18 lacking CVE identifiers, affecting devices from multiple major vendors, and signifying a shift to multivector operations.
- Widespread DDoS Activity: The botnet AISURU, built on Mirai, represents a major threat, leveraging compromised IoT devices for record-setting DDoS attacks, with origins primarily traced to various countries, including Brazil and China.
RondoDox Botnet Expands Attack Surface
Malware campaigns have intensified with the emergence of the RondoDox botnet. Researchers warn that it exploits over 50 security flaws, spanning more than 30 vendors. This “exploit shotgun” approach targets various devices such as routers, digital video recorders (DVRs), and more. Consequently, organizations must be vigilant. For example, a recent attack targeted TP-Link Archer routers using CVE-2023-1389, a vulnerability under active exploitation since late 2022.
Initially documented in July 2025, the RondoDox botnet gained attention for its coordinated attacks on DVRs and routers. Now, it utilizes a “loader-as-a-service” model, complicating detection efforts. The botnet’s arsenal includes 56 vulnerabilities, with a significant number lacking a CVE identifier. As a result, security experts view this evolution as a significant threat. Observers emphasize that RondoDox signifies the transition from opportunistic hacking to a more organized, multi-directional attack strategy, raising concerns across the cybersecurity landscape.
Growing Threat and Network Exploitation
In recent months, the RondoDox botnet’s distribution strategy evolved to encompass broader attack vectors. Reports from cybersecurity firms revealed a large-scale distribution through IoT devices and enterprise applications. By exploiting weak credentials and known vulnerabilities, RondoDox poses a considerable risk. Security journalist analyses indicate that similar botnets, such as AISURU, have gained notoriety, drawing power from compromised IoT devices on networks like AT&T and Verizon.
Moreover, the emergence of orchestrated attacks targeting Remote Desktop Protocol (RDP) services emphasizes the growing complexity of these threats. Coordinated actions involving over 100,000 unique IP addresses across numerous countries further underline the severity. Observers note that centralized control likely fuels many of these efforts, as evidenced by shared TCP fingerprints among participating IPs. As cybersecurity continues to face evolving challenges, vigilance and proactive measures will be crucial to mitigate the risks posed by RondoDox and similar threats.
Continue Your Tech Journey
Stay informed on the revolutionary breakthroughs in Quantum Computing research.
Discover archived knowledge and digital history on the Internet Archive.
DataProtection-V1