Top Highlights
-
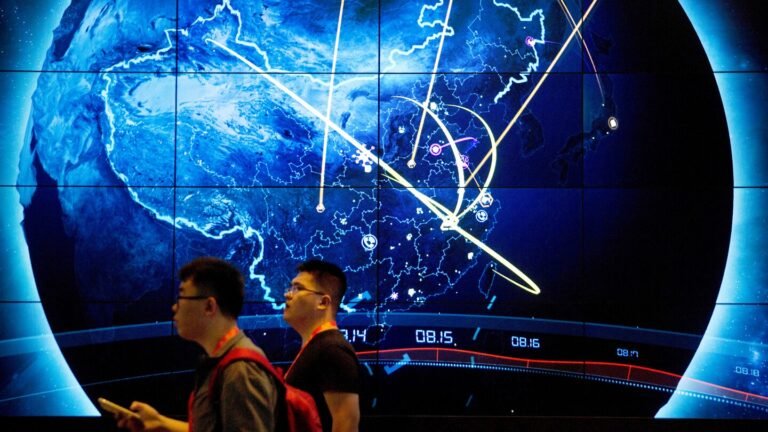
Accusation of Cyberattacks: China has accused the U.S. National Security Agency of cyberattacks on its national time center, claiming this could have disrupted critical infrastructure.
-
Exploitation of Vulnerabilities: The Chinese Ministry of State Security alleges that the NSA exploited messaging service vulnerabilities to steal sensitive information in 2022.
-
Advanced Cyberattack Tools: The NSA reportedly used 42 types of cyberattack tools to target the time center’s internal systems and attempted infiltration of crucial timing systems between 2023 and 2024.
- Rising Tensions: This accusation may escalate existing tensions between the U.S. and China, already strained due to issues in trade, technology, and Taiwan.
[gptA technology journalist, write a short news story divided in two subheadings, at 12th grade reading level about ‘China accuses US of cyberattack on national time center’in short sentences using transition words, in an informative and explanatory tone, from the perspective of an insightful Tech News Editor, ensure clarity, consistency, and accessibility. Use concise, factual language and avoid jargon that may confuse readers. Maintain a neutral yet engaging tone to provide balanced perspectives on practicality, possible widespread adoption, and contribution to the human journey. Avoid passive voice. The article should provide relatable insights based on the following information ‘
BEIJING (AP) — China on Sunday accused the U.S. National Security Agency of carrying out cyberattacks on its national time center following an investigation, saying any damage to related facilities could have disrupted network communications, financial systems and power supply.
The Ministry of State Security alleged in a WeChat post that the U.S. agency had exploited vulnerabilities in the messaging services of a foreign mobile phone brand to steal sensitive information from devices of the National Time Service Center’s staff in 2022. It did not specify the brand.
The U.S. agency also used 42 types of “special cyberattack weapons” to target the center’s multiple internal network systems and attempted to infiltrate a key timing system between 2023 and 2024, it said.
It said it had evidence but did not provide it in the post.
It said the time center is responsible for generating and distributing China’s standard time, in addition to providing timing services to industries such as communications, finance, power, transport and defense. It had provided guidance to the center to eliminate the risks.
“The U.S. is accusing others of what it does itself, repeatedly hyping up claims about Chinese cyber threats,” it said.
Western governments in recent years have alleged hackers linked to the Chinese government have targeted officials, journalists, corporations and others. The ministry’s statement could fuel tensions between Washington and Beijing, on top of trade, technology and Taiwan issues.
The U.S. Embassy did not immediately comment.
‘. Do not end the article by saying In Conclusion or In Summary. Do not include names or provide a placeholder of authors or source. Make Sure the subheadings are in between html tags of
[/gpt3]
Continue Your Tech Journey
Learn how the Internet of Things (IoT) is transforming everyday life.
Stay inspired by the vast knowledge available on Wikipedia.
Cybercrime-V1