Quick Takeaways
- Cyberangriffe auf deutsche Unternehmen, die auf Leak-Seiten veröffentlicht werden, haben sich zwischen 2021 und 2024 vervierfacht, Deutschland ist dabei Spitzenreiter.
- Laut BKA richten sich 80% der 950 analysierten Ransomware-Angriffe im Jahr 2024 gegen kleine und mittlere Unternehmen.
- In 251 Fällen wurde durch ransomware.live ein Datenabfluss nachgewiesen, was die Bedrohung durch Datenverlust unterstreicht.
- Angreifer setzen hauptsächlich auf Double Extortion, bei der Daten zuerst verschlüsselt und dann mit Veröffentlichung bedroht werden.
The Core Issue
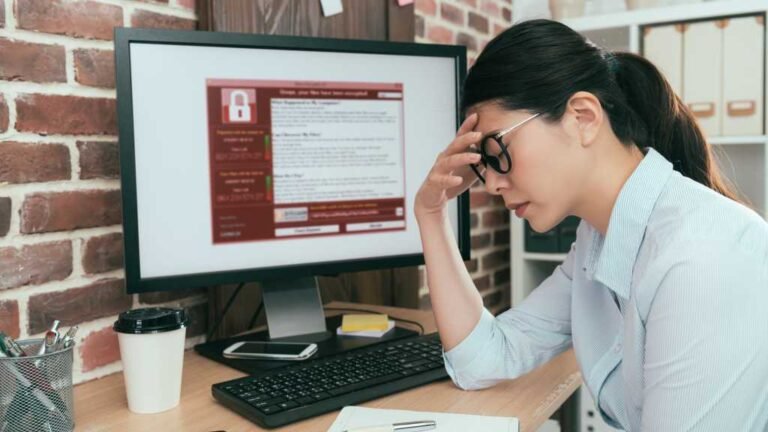
Cyberangriffe auf deutsche kleine und mittlere Unternehmen (KMUs) haben zwischen 2021 und 2024 eine drastische Zunahme erlebt, mit einer mehr als vierfachen Steigerung der Angriffe, die auf Leak-Seiten veröffentlicht wurden. Deutschland führt die Liste der Länder mit den meisten Fällen an, gefolgt von Italien, Frankreich und Spanien. Laut dem Bundeskriminalamt (BKA) sind 80 Prozent der 950 untersuchten Ransomware-Angriffe im Jahr 2024 gezielt gegen KMUs gerichtet, wobei in 251 Fällen ein Datenleck nachgewiesen werden konnte. Die Angreifer setzen dabei meist die Methode des Double Extortion ein, bei der zuerst die Daten verschlüsselt werden und anschließend mit der Veröffentlichung der gestohlenen Informationen gedroht wird, um Druck auf die Unternehmen auszuüben und Zahlungen zu erzwingen. Diese Entwicklungen werden von der Transferstelle Cybersicherheit im Mittelstand berichtet, die die alarmierende Zunahme und die Methoden der Angreifer dokumentiert.
Security Implications
Cyber risks pose a significant threat to businesses, especially small and medium-sized enterprises (SMEs), which are increasingly targeted by ransomware attacks; from 2021 to 2024, cyberattacks involving leaked data on public leak sites have surged more than fourfold in Germany, positioning it as a European leader in such incidents. According to the Federal Criminal Police Office (BKA), 80% of the 950 ransomware assaults evaluated in 2024 targeted SMEs, with evidence of data exfiltration in over 250 cases. Attackers frequently employ double extortion tactics—first encrypting the data, then threatening to publish the stolen information—causing severe operational disruptions, financial losses, reputational damage, and data privacy breaches, thereby highlighting the escalating severity and complexity of cyber threats facing organizations across industries.
Possible Remediation Steps
Understanding the urgency of prompt action is crucial when facing the escalating cyber threats targeting small and medium-sized enterprises (SMEs). Swift remediation efforts can significantly reduce potential damage, protect sensitive data, and ensure business continuity in an increasingly hostile digital landscape.
Mitigation Strategies
- Implement robust firewalls and anti-malware solutions to prevent unauthorized access and detect malicious activity early.
- Conduct regular security assessments to identify vulnerabilities in systems and applications.
- Educate staff on cybersecurity best practices, including recognizing phishing attempts and managing passwords securely.
Remediation Steps
- Isolate affected systems immediately to contain the threat and prevent lateral movement within the network.
- Apply necessary patches and updates to close security gaps exploited by attackers.
- Perform comprehensive data backups and establish recovery procedures to restore operations swiftly after an incident.
- Engage cybersecurity professionals or incident response teams to analyze the breach and strengthen defenses against future attacks.
Advance Your Cyber Knowledge
Explore career growth and education via Careers & Learning, or dive into Compliance essentials.
Understand foundational security frameworks via NIST CSF on Wikipedia.
Disclaimer: The information provided may not always be accurate or up to date. Please do your own research, as the cybersecurity landscape evolves rapidly. Intended for secondary references purposes only.
Cyberattacks-V1