Fast Facts
- A new cyberthreat campaign, ClickFix, impersonates trusted sources like BBC and Cloudflare, tricking users into executing malicious commands via fake verification screens.
- The attack leverages convincing counterfeit websites and social engineering tactics, prompting users to run embedded PowerShell commands that download malware, including ransomware and info stealers.
- The campaign surged over 517% in early 2025, with variants targeting multiple platforms and using sophisticated evasion techniques, making detection difficult across conventional security tools.
- To mitigate: avoid executing unsolicited commands, disable risky features like the Windows Run dialog, train users to recognize suspicious prompts, and maintain updated security defenses with behavioral analysis.
The Issue
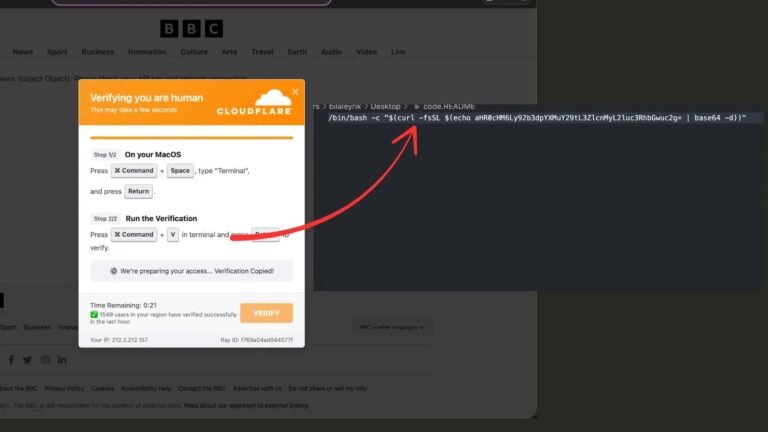
In 2024 and 2025, a sophisticated cyber threat known as the ClickFix attack has rapidly increased, posing a significant danger to both individuals and organizations. This campaign involves impersonating trusted news sources like the BBC through convincingly fake websites, which then redirect users to counterfeit Cloudflare security verification pages. These pages look identical to authentic ones, tricking users into believing they are completing legitimate security checks. When users attempt to verify themselves by clicking the “Verify you are human” checkbox, malicious PowerShell commands are secretly loaded into their clipboard. If pasted and executed, these commands download malware varieties such as ransomware, remote access trojans, and info-stealers. The attack’s success relies heavily on social engineering, exploiting users’ urgency to resolve perceived technical issues, enabling cybercriminals to bypass traditional security measures with remarkably evasive and well-crafted deception.
The creators of ClickFix have adapted their techniques to impersonate multiple trusted entities beyond the BBC, including tech giants like Microsoft and Google, expanding their reach. Their malware is designed to evade detection with anti-analysis features and sophisticated payloads, making the attack both complex and dangerous. Security researchers underline that platforms like Cloudflare never require direct user interaction or terminal commands, and any such requests should be treated as suspicious. In response, cybersecurity professionals recommend better user education, disabling certain system functionalities, and deploying advanced monitoring tools to reduce the risk. As these attacks evolve and grow more cunning, heightened awareness and robust protective measures remain paramount to defend against this emerging threat landscape.
Critical Concerns
A highly sophisticated cyberattack, known as the ClickFix campaign, has rapidly increased in prevalence, with over a 517% rise in 2025, exploiting human psychology and trust through imposter news sites and fabricated security prompts. Attackers impersonate trusted sources such as BBC and mimic legitimate Cloudflare verification pages, luring users into executing malicious PowerShell commands under the guise of routine security checks. When users follow these prompts, they inadvertently download and run malware variants—including ransomware, info stealers, and remote access Trojans—often obfuscated with anti-analysis features and encrypted payloads to evade detection. These attacks leverage social engineering, capitalizing on users’ urgency to fix technical issues, and employ highly convincing visual replicas to deceive even vigilant users. The result is a severe threat landscape where malware can compromise systems, steal sensitive data, or facilitate remote control, highlighting the critical importance of user education, cautious interaction with security prompts, and robust detection strategies—since conventional security defenses often fall short against these adaptive, deception-based tactics.
Possible Action Plan
In the rapidly evolving landscape of cyber threats, prompt remediation is vital to prevent widespread harm, protect sensitive information, and restore trust. Addressing issues like the "New ClickFix Attack Uses Fake BBC News Page and Fraudulent Cloudflare Verification" quickly can minimize damage, halt the spread of malicious activity, and preserve organizational integrity.
Mitigation Strategies
- Identify Source: Conduct thorough analysis to determine the origin of the fake pages and malicious links.
- Update Filters: Implement real-time URL filtering and block suspicious domains.
- Strengthen Verification: Enhance website verification protocols, including DNS and SSL checks.
- Alert Users: Inform users about ongoing threats and advise caution when clicking suspicious links.
- Deploy Security Tools: Utilize web application firewalls (WAFs) and anti-malware solutions.
- Report Incidents: Notify relevant authorities and platforms such as Cloudflare and BBC about the malicious activity.
- Remove Threats: Take down or isolate fake pages and malicious content swiftly.
- Review Security Posture: Conduct comprehensive security audits to identify vulnerabilities.
- Educate Staff: Provide ongoing cybersecurity training to recognize and respond to phishing and scam tactics.
- Monitor Continuously: Set up continuous monitoring for emerging threats and suspicious activity to enable rapid response.
Stay Ahead in Cybersecurity
Stay informed on the latest Threat Intelligence and Cyberattacks.
Learn more about global cybersecurity standards through the NIST Cybersecurity Framework.
Disclaimer: The information provided may not always be accurate or up to date. Please do your own research, as the cybersecurity landscape evolves rapidly. Intended for secondary references purposes only.
Cyberattacks-V1