Despite the hours of security awareness training that employees undergo, they still click on credential phishing links at an alarming rate. Once they enter their credentials, cybercriminals gain immediate access to their email accounts.
From there, these criminals can cause a variety of havoc, such as stealing sensitive data, accessing other applications, or using the compromised account to send malicious emails to customers, vendors, or fellow employees.
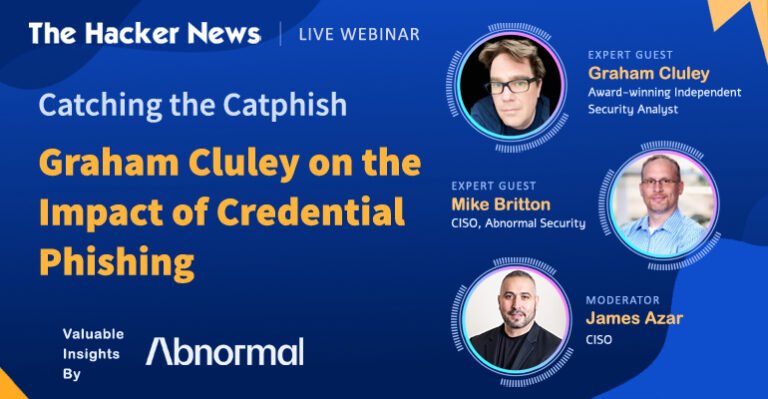
Join this webinar with Graham Cluley, the host of the Smashing Security podcast, and Abnormal Security CISO Mike Britton to learn about:
How attackers lure their victims into submitting credentials, including through the use of generative AI.
The reasons victims keep falling for the bait, and why security awareness training fails to prevent it.
Strategies for dealing with malicious actors once they have gained access.
Essential tools needed to combat the phishing problem before encountering murky waters.