Fast Facts
- Cybersecurity researchers reveal a novel Linux malware delivery method via phishing emails containing RAR archives with filenames embedded with malicious Bash code, evading traditional antivirus scans.
- The attack’s payload involves decoding and executing a Base64-encoded downloader that retrieves and runs a Linux backdoor called VShell, capable of full remote system control.
- The phishing email disguises as a beauty survey offering monetary rewards, leveraging social engineering, with the malicious file only executing when parsed by a shell script.
- Recent developments include advanced Linux tools like RingReaper, which use the kernel’s io_uring framework to evade detection and perform stealthy post-exploitation activities.
Problem Explained
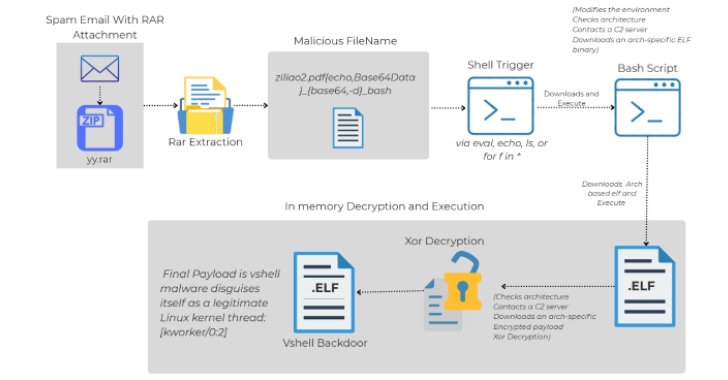
Cybersecurity experts have uncovered a sophisticated new attack method involving phishing emails crafted to deliver a Linux-specific backdoor called VShell. The attack begins with a seemingly innocuous email promising a monetary reward for a survey, but it secretly contains a RAR archive with a maliciously named file embedded with shell code. This filename, which appears innocent but is cleverly encoded, triggers malicious activity only when parsed by a shell script, exploiting a vulnerability where filenames are not properly sanitized. Once the file is extracted, it doesn’t execute immediately; instead, it activates a chain of commands, involving Base64 decoding and external server communication, ultimately downloading and executing a powerful malware payload that grants remote control over Linux systems. This malware operates entirely in memory, making it especially difficult to detect with traditional security tools, and targets a broad range of Linux devices, including those used by Chinese hacking groups.
The report, authored by Trellix researchers, emphasizes that the attack’s ingenuity lies in weaponizing filename encoding to bypass antivirus detection—since most defenses overlook filename-based threats—and in exploiting common scripting vulnerabilities. Meanwhile, additional insights from Picus Security detail a related Linux malware tactic called RingReaper, which uses advanced Linux kernel features to evade detection and maintain persistence. Overall, these developments highlight an alarming evolution in Linux-targeted cyber threats, combining social engineering with complex, stealthy malware deployment strategies capable of enabling extensive system control without leaving conventional traces.
Critical Concerns
Cybersecurity experts have revealed increasingly sophisticated Linux malware attack chains, exemplified by a recent campaign using phishing emails to deliver an open-source backdoor called VShell, via malicious RAR archives with filenames that embed encoded Bash commands. These filenames exploit command injection vulnerabilities, allowing remote code execution without triggering traditional detection mechanisms, as antivirus software typically ignores filename-based threats. Once activated, the malware retrieves an external ELF binary, establishing communication with command-and-control servers to deploy the VShell backdoor, granting attackers extensive remote control, including file operations, process management, and encrypted communications. Such stealthy, memory-resident malware bypasses disk-based defenses and can target a vast array of Linux devices, illustrating a dangerous evolution in cyber threats that leverage Linux’s permissiveness, subtle social engineering, and sophisticated payload delivery techniques, thereby significantly amplifying the potential impact—ranging from data theft and system disruption to sustained espionage—that organizations must now contend with in protecting their digital infrastructure.
Possible Remediation Steps
Addressing Linux malware delivered through malicious RAR filenames that evade antivirus detection is crucial to maintaining system integrity and preventing widespread damage. Prompt and effective remediation ensures that threats are contained before they infiltrate deeper into the environment, safeguarding sensitive data and avoiding prolonged operational disruptions.
Mitigation Strategies
- Conduct comprehensive system scans using updated, specialized malware detection tools tailored for Linux environments.
- Monitor and analyze network traffic for unusual or unauthorized data exfiltration activities.
- Remove malicious RAR files and related artifacts immediately upon detection.
- Restrict the use of unnecessary RAR and other archive file handling permissions to limit threat vectors.
- Implement application whitelisting to prevent execution of unauthorized or suspicious files.
Remediation Steps
- Isolate infected systems from the network to prevent malware spread.
- Remove malicious files and associated payloads identified during scans.
- Apply the latest security patches and updates to the Linux operating system and relevant software.
- Reset affected user credentials and review access controls for vulnerabilities.
- Enhance monitoring protocols to detect future anomalous activities and improve incident response plans.
Stay Ahead in Cybersecurity
Explore career growth and education via Careers & Learning, or dive into Compliance essentials.
Learn more about global cybersecurity standards through the NIST Cybersecurity Framework.
Disclaimer: The information provided may not always be accurate or up to date. Please do your own research, as the cybersecurity landscape evolves rapidly. Intended for secondary references purposes only.
Cyberattacks-V1