-
Collaboration in Cybersecurity: The Microsoft Security Excellence Awards celebrate global teamwork in cybersecurity, emphasizing that success hinges on collective efforts to combat evolving threats.
-
Recognition of Innovators: On January 26, 2026, leaders in security innovation were honored, showcasing contributions from partners and individuals making substantial impacts in cybersecurity.
-
Award Categories: Key award categories included Security Trailblazer, Data Security and Compliance Trailblazer, Secure Access Trailblazer, Security Changemaker, Security Software Development Company of the Year, and Security Services Partner of the Year, with notable winners in each.
-
Commitment to a Safer Future: The initiative aims to foster ongoing collaboration and innovation, driving towards a more resilient digital environment for all stakeholders in the cybersecurity landscape.
Recognizing Collaboration in Cybersecurity
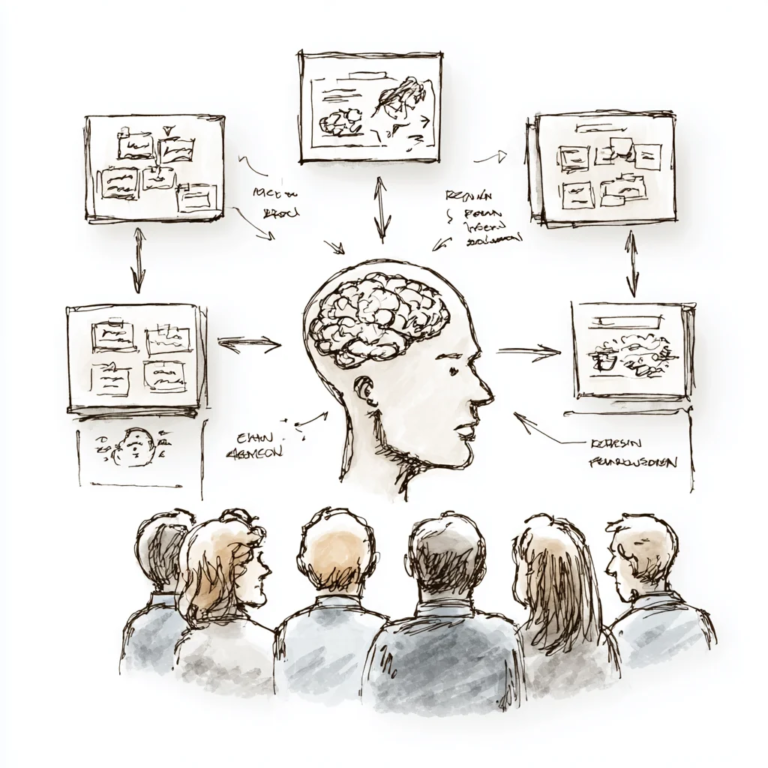
In a world dominated by cyber threats, collaboration stands at the forefront of cybersecurity innovation. Microsoft recently honored the 2026 Security Excellence Awards winners, highlighting the importance of teamwork and shared expertise. These awards shine a spotlight on organizations that embody this spirit. They illustrate how diverse skills and knowledge combine to tackle complex challenges.
Winners like Avertium and BlueVoyant have set new standards in security practices. Their focus on AI-powered solutions demonstrates that effective defense requires creativity and technology. Their innovations resonate beyond the competition, influencing how enterprises implement security measures. This recognition encourages companies to look for partnerships, fostering a culture of shared responsibility in cybersecurity.
Practical Implications for Day-to-Day Operations
The impact of these award winners on daily IT operations cannot be understated. For example, organizations can adopt Zero Trust strategies, inspired by leaders like Tata Consultancy Services. This approach enhances security by ensuring that every access request is verified, minimizing potential breaches. With such frameworks in place, companies can better manage their vulnerabilities.
Moreover, utilizing AI technologies can streamline threat detection and response times. As showcased by various winners, these advancements can significantly improve incident response strategies. Therefore, organizations should actively assess their cybersecurity tools and consider integrating top-tier solutions that have proven effective in real-world applications.
As teams embrace the lessons learned from these innovators, they contribute to a more resilient digital landscape. The collaborative efforts recognized at the awards serve as a reminder that in cybersecurity, strength lies in unity. By working together, enterprises can build a safer environment for everyone.
Expand Your Tech Knowledge
Get real-time Cyber Updates on threats, defenses, and industry shifts.
Access comprehensive resources on technology by visiting Wikipedia.
Expert Insights