Summary Points
-
High-Severity Vulnerability: A critical security flaw (CVE-2025-59363) in One Identity OneLogin’s IAM solution exposes sensitive OpenID Connect client secrets, rated 7.7/CVSS.
-
Exploitation Method: Attackers with valid API credentials can retrieve client secrets by accessing the misconfigured /api/2/apps endpoint, risking unauthorized data access and impersonation of applications.
-
Widespread Risk: The flaw enables lateral movement within the OneLogin platform due to broad API access and lack of IP allowlisting, making it exploitable from anywhere globally.
- Mitigation and Awareness: OneLogin addressed the vulnerability in version 2025.3.0 by concealing OIDC client secrets, highlighting the critical need for robust API security in identity management systems.
High-Severity Vulnerability Discovered
A significant security flaw emerged within the One Identity OneLogin Identity and Access Management (IAM) solution. This vulnerability, identified as CVE-2025-59363, received a CVSS score of 7.7 out of 10.0, indicating its severity. Researchers explained that this issue pertains to incorrect resource transfer, which compromises security boundaries and permits unauthorized access to sensitive data.
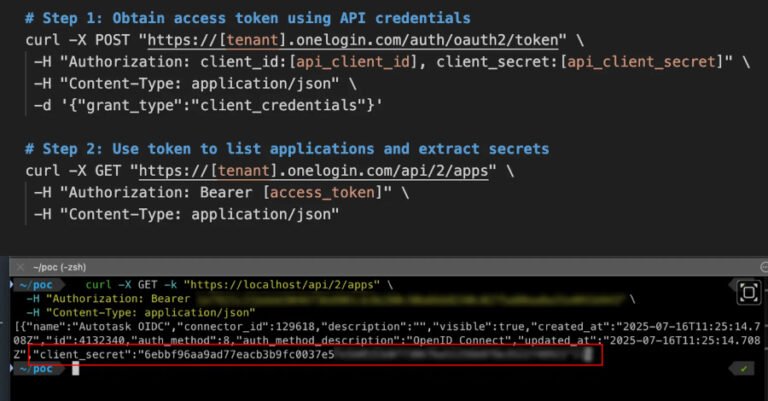
According to a report, the vulnerability permitted attackers with valid API credentials to access confidential OpenID Connect (OIDC) application client secrets on a company’s OneLogin account. Specifically, the flaw arose because the application listing endpoint returned excessive data. This data included valuable client secret values, alongside app metadata, making it easier for attackers to exploit the system.
Potential Consequences and Resolution
If successful, an attack could lead to serious implications. An attacker could utilize exposed client secrets to impersonate applications, gaining access to integrated services. Furthermore, the role-based access control mechanism allowed compromised API keys to reach numerous sensitive endpoints, amplifying the risk.
The absence of IP address allowlisting complicated the situation as attackers could exploit the vulnerability globally. However, after responsible disclosure on July 18, 2025, OneLogin promptly rolled out a fix in version 2025.3.0, which ensured OIDC client_secret values were no longer visible. Fortunately, there is no indication that this vulnerability was exploited in the wild.
The incident underscores the importance of robust API security in identity management systems. The ramifications of such vulnerabilities can affect entire technology stacks, emphasizing a need for constant vigilance and enhancement in security measures.
Stay Ahead with the Latest Tech Trends
Learn how the Internet of Things (IoT) is transforming everyday life.
Access comprehensive resources on technology by visiting Wikipedia.
DataProtection-V1