Top Highlights
-
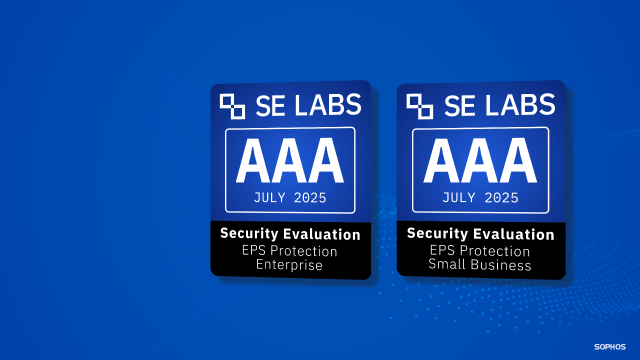
AAA Ratings Achieved: Sophos Endpoint has earned AAA ratings from SE Labs in both Small Business and Enterprise categories for Q2 2025, marking three consecutive years of top performance in real-world and simulated cyberattack detection.
-
Advanced Security Features: Sophos Endpoint employs a prevention-first strategy with multiple AI models to combat known and novel threats, extensive controls to minimize attack surfaces, and advanced technologies to quickly neutralize threats.
-
Significance of Third-Party Testing: SE Labs provides crucial, realistic evaluations of cybersecurity tools, using modern attack techniques, thus helping organizations make informed decisions about their security investments.
- Recognition and Leadership: Recently awarded four accolades at the SE LABS ® Awards 2025, Sophos also stands out as the only vendor named a Leader across multiple G2 reports, ranking #1 in 36 categories based on user feedback.
Problem Explained
In its Q2 2025 Endpoint Protection report, SE Labs has highlighted Sophos Endpoint’s remarkable achievement, awarding it AAA ratings in both Small Business and Enterprise categories. This recognition underscores Sophos’s unwavering commitment to thwarting cyber threats by employing a robust, multi-faceted approach to security—interwoven with advanced AI technology that preemptively addresses both known and novel attacks. SE Labs, known for its rigorous simulation of contemporary cybercriminal tactics, has consistently validated Sophos’s efficacy in real-world scenarios, positioning it as a leading guardian in the cybersecurity landscape.
The announcement arrives following Sophos’s commendable performance at the SE LABS Awards 2025 in London, where it secured four awards, emphasizing its dedication to providing top-tier protection across various business segments. Moreover, Sophos maintains its status as a frontrunner in the G2 Overall Grid® Reports, showcasing its leadership across multiple cybersecurity domains based on user feedback. Such accolades not only enhance Sophos’s reputation but also assist organizations in making informed security investments in an increasingly perilous digital environment.
Risk Summary
The recent accolades awarded to Sophos Endpoint by SE Labs underscore its robust capabilities in thwarting cyber threats, an outcome that, while commendable, raises critical implications for other businesses, users, and organizations that may not employ similarly advanced protections. As cyberattacks continue to escalate in both frequency and sophistication, the reliance on less effective or outdated security measures could expose these entities to heightened vulnerabilities and potentially catastrophic breaches. Such incidents not only compromise sensitive data and disrupt operations but can also culminate in significant financial losses and reputational damage that ripple through the broader market ecosystem. In a landscape where attackers increasingly exploit the weakest links, organizations that fail to adopt cutting-edge security solutions risk becoming conduits for widespread compromise, ultimately jeopardizing their relationships with clients, partners, and stakeholders. The differentiated performance of market leaders like Sophos thus highlights the imperative for businesses to invest in advanced cybersecurity strategies, ensuring they do not inadvertently contribute to a collective vulnerability that undermines the integrity of the entire digital landscape.
Possible Remediation Steps
Timely remediation is crucial in maintaining security and trust within digital environments, especially in the context of ‘Consistently AAA Rated – Q2 2025 SE Labs Endpoint Protection Report – Sophos News.’ Addressing vulnerabilities promptly is essential to safeguarding sensitive information and ensuring robust protection against evolving threats.
Mitigation Measures
-
Regular Updates
Ensure all endpoint protection software is current, incorporating the latest patches and definitions. -
User Training
Conduct ongoing training sessions to educate employees about cybersecurity best practices and phishing awareness. -
Incident Response Plan
Develop and routinely test a comprehensive incident response plan to address potential breaches swiftly. -
Enhanced Monitoring
Implement continuous monitoring systems to detect and respond to anomalies in real-time. - Vulnerability Assessment
Perform regular assessments to identify and prioritize system vulnerabilities for remediation.
NIST CSF Guidance
The NIST Cybersecurity Framework (CSF) emphasizes proactive risk management and the importance of timely remediation. Specifically, refer to the "Protect" and "Respond" functions of the framework. For further details, explore the NIST Special Publication (SP) 800-53, which provides comprehensive guidelines on security and privacy controls for federal information systems and organizations.
Continue Your Cyber Journey
Explore career growth and education via Careers & Learning, or dive into Compliance essentials.
Explore engineering-led approaches to digital security at IEEE Cybersecurity.
Disclaimer: The information provided may not always be accurate or up to date. Please do your own research, as the cybersecurity landscape evolves rapidly. Intended for secondary references purposes only.
Cyberattacks-V1