Fast Facts
- Integrating high-fidelity threat intelligence feeds into SOC tools significantly reduces Mean Time to Detect (MTTD) and false positives by providing validated, high-confidence alerts enriched with contextual data.
- High-quality threat intel curates verified IOCs, which help eliminate ambiguous alerts, allowing automated responses and decreasing alert fatigue, analyst burnout, and resource wastage.
- Contextual enrichments—such as threat categorization, severity scores, and related artifacts—transform generic alerts into actionable insights, improving detection accuracy and reducing false positives.
- Threat intelligence empowers proactive threat hunting and automates initial triage, enabling SOC teams to focus on complex threats, shorten response times, and strengthen overall security posture.
Problem Explained
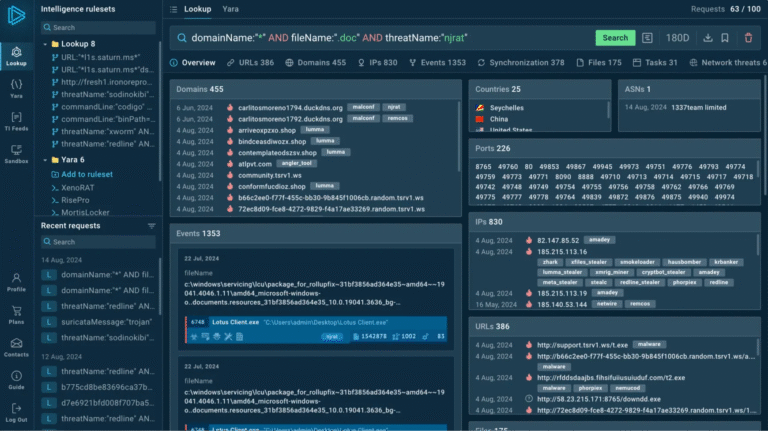
The story recounts how Security Operations Centers (SOCs) are increasingly relying on high-quality threat intelligence (TI) feeds to bolster their defenses against cyber threats. These feeds provide real-time Indicators of Compromise (IOCs), which, when integrated into security tools like SIEMs, drastically cut down the time it takes to detect an attack—thereby lowering the Mean Time to Detect (MTTD). The improved detection efficiency also leads to fewer false positives, which are mistaken alerts that flag harmless activity as malicious. False positives have been a major challenge, causing alert fatigue, wasting resources, and eroding trust among security analysts. By utilizing vetted, high-fidelity TI feeds that include detailed context such as threat categorization, severity scores, and related artifacts, SOCs can better differentiate genuine threats from noise, automating responses to known malicious activity and freeing analysts to focus on more complex issues. This dual approach of rapid detection and reduced false alarms not only enhances the organization’s security posture but also improves proactive threat hunting, ultimately making organizations more resilient against advanced cyberattacks. The reporting emphasizes that leveraging these high-quality, real-time threat intelligence feeds considerably improves SOC performance, as evidenced by reductions in both detection time and false positives, benefiting organizations seeking a more efficient and trustworthy cybersecurity operation.
What’s at Stake?
Cyber risks pose significant threats to organizational assets, with Security Operations Centers (SOCs) serving as critical defensive hubs that leverage metrics like Mean Time to Detect (MTTD) and False Positive Rate (FPR) to gauge effectiveness. High FPR undermines SOC performance by flooding analysts with irrelevant alerts, leading to alert fatigue, wasted resources, and diminished trust in security tools, while a low MTTD is vital for timely threat neutralization, minimizing attacker dwell time. Integrating high-quality, real-time Threat Intelligence (TI) feeds—containing validated Indicators of Compromise (IOCs), threat context, and Tactics, Techniques, and Procedures (TTPs)—enhances detection accuracy, cuts down false positives, and accelerates response times from hours to seconds. This synergy enables automated triage, better resource allocation for threat hunting, and a proactive security stance, collectively reducing cyber risks’ damage and reinforcing organizational resilience against evolving cyber threats.
Possible Actions
Promptly addressing cyber threats identified through threat intelligence feeds is crucial for safeguarding sensitive data and maintaining operational continuity. The ability of SOC teams to rapidly detect and remediate threats minimizes potential damage, reduces recovery time, and prevents adversaries from exploiting vulnerabilities.
Mitigation Strategies:
- Confirm Threats
- Isolate Affected Systems
- Apply Security Patches
- Quarantine Malicious Files
- Disable Vulnerable Services
Remediation Steps:
- Conduct Forensic Analysis
- Remove Malicious Artifacts
- Reset Compromised Credentials
- Update Detection Rules
- Monitor Post-Remediation Activity
Explore More Security Insights
Discover cutting-edge developments in Emerging Tech and industry Insights.
Access world-class cyber research and guidance from IEEE.
Disclaimer: The information provided may not always be accurate or up to date. Please do your own research, as the cybersecurity landscape evolves rapidly. Intended for secondary references purposes only.
Cyberattacks-V1