Quick Takeaways
-
Targeted Cyber Attacks: A China-linked cyber espionage group has launched two campaigns, Operation GhostChat and Operation PhantomPrayers, against the Tibetan community ahead of the Dalai Lama’s 90th birthday, utilizing compromised websites for malware distribution.
-
Malware Techniques: Both operations deploy advanced malware, including Gh0st RAT and PhantomNet, through watering hole attacks that infect devices of users visiting specific, compromised sites.
-
Deceptive Messaging Platforms: Attackers disguised malicious tools as secure chat applications and check-in apps to collect sensitive user information and promote malware installation under the guise of sending blessings to the Dalai Lama.
- Staying Stealthy: The malware features advanced capabilities like remote access, file manipulation, and covert operations, allowing it to manage compromised systems without detection by utilizing encrypted communication and modular payloads.
Underlying Problem
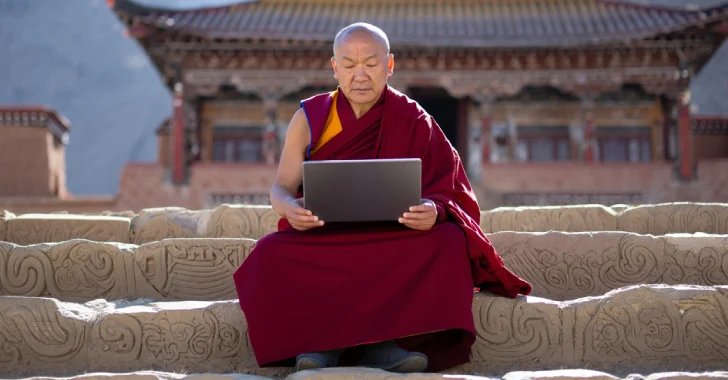
In July 2025, the Tibetan community became the target of sophisticated cyber espionage campaigns orchestrated by a group linked to China, as part of a strategic effort coinciding with the Dalai Lama’s 90th birthday. Named Operations GhostChat and PhantomPrayers by Zscaler ThreatLabz, these attacks employed a technique known as “watering hole attacks,” where attackers infiltrate websites frequented by specific groups to deploy malicious software. The attackers compromised a legitimate webpage meant for messages to the Dalai Lama, substituting it with a fraudulent site that unwittingly encouraged users to download a malicious chat application, TElement, laden with the Gh0st RAT, a potent remote access trojan favored by Chinese hacking factions.
Security researchers Sudeep Singh and Roy Tay reported that this assault was not an isolated incident; in fact, it mirrored past incursions by various hacking groups—such as EvilBamboo and Evasive Panda—that have consistently targeted the Tibetan diaspora to extract sensitive information. The second phase, Operation PhantomPrayers, further entangled victims by offering a deceptive “90th Birthday Global Check-in” application, which while seemingly innocuous, stealthily installed the PhantomNet backdoor, facilitating ongoing access to compromised systems through modular plugins. This multi-layered approach not only exemplified the challenges of cyber defense but also underscored the persistent vulnerabilities faced by the Tibetan community.
Security Implications
The recent cyber espionage campaigns targeting the Tibetan community, specifically Operations GhostChat and PhantomPrayers, pose significant risks not only to the victims but also to various interconnected businesses, users, and organizations. As threat actors leverage watering hole attacks to inject malware (such as Gh0st RAT and PhantomNet) through compromised legitimate websites, the potential for broader collateral damage becomes evident. Businesses that overlap with the Tibetan diaspora or support related initiatives risk having sensitive data and business operations compromised, leading to financial losses, eroded trust, and reputational damage. Additionally, users who inadvertently engage with infected software may unwittingly become conduits for the malware, facilitating the spread of cyber threats across networks. Organizations must remain vigilant, as the cascading effects of these cyber intrusions can reverberate through supply chains, impacting operational integrity and cybersecurity posture across multiple sectors.
Possible Remediation Steps
In an era defined by technological interconnectivity, the imperative for swift and effective remediation against cyber threats has never been more pronounced, particularly regarding nation-state actors targeting vulnerable communities.
Mitigation Strategies
- Immediate App Removal
- User Education Initiatives
- Enhanced Cybersecurity Protocols
- Incident Response Plans
- Regular Software Updates
- Vulnerability Assessments
- Data Encryption Practices
- Collaborative Threat Intelligence Sharing
NIST CSF Guidance
The NIST Cybersecurity Framework emphasizes a proactive, risk-based approach to cybersecurity. Recommended documents include NIST SP 800-53 for comprehensive security and privacy controls, as well as NIST SP 800-37 for managing risk through the Risk Management Framework (RMF).
Advance Your Cyber Knowledge
Explore career growth and education via Careers & Learning, or dive into Compliance essentials.
Access world-class cyber research and guidance from IEEE.
Disclaimer: The information provided may not always be accurate or up to date. Please do your own research, as the cybersecurity landscape evolves rapidly. Intended for secondary references purposes only.
Cyberattacks-V1