Essential Insights
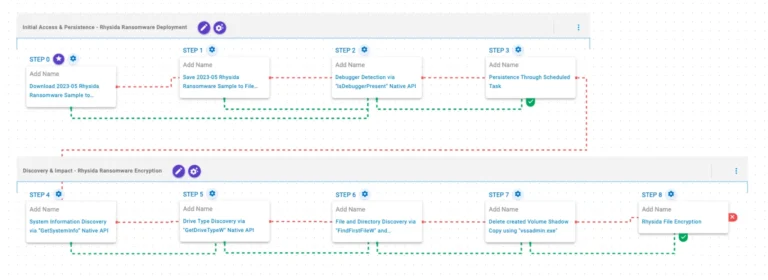
- AttackIQ’s Ransom Tales series emulates TTPs of prominent ransomware families (Rhysida, Charon, Dire Wolf) to enable organizations to validate and enhance their security controls against evolving threats.
- Each ransomware emulation reveals detailed operational behaviors—like initial access, persistence, discovery, encryption, and defense evasion—allowing targeted testing of detection and prevention mechanisms.
- The ransomware strains employ advanced tactics such as DLL sideloading, process injection, EDR bypasses, live data exfiltration, and disruptive techniques like shadow copy deletion and log clearing.
- Continuous testing using these emulations equips security teams to improve incident response, reduce risk exposure, and adapt defenses against both opportunistic and targeted cyber extortion campaigns.
The Issue
On July 22, 2025, AttackIQ launched its Ransom Tales initiative, a series of sophisticated simulations that emulate the tactics, techniques, and procedures (TTPs) used by prominent ransomware families—including Rhysida, Charon, and Dire Wolf—aimed at helping organizations evaluate and strengthen their cybersecurity defenses. The latest installment employs detailed attack graphs that replicate how these ransomware strains infiltrate systems, execute their malicious payloads, and deploy destruction tactics such as file encryption, data exfiltration, and system sabotage. For instance, Rhysida operates as a ransomware-as-a-service, gaining initial access through remote services or phishing, then using tools like Cobalt Strike, PowerShell, and PsExec to maintain persistence and escalate privileges before encrypting files with robust algorithms, notably targeting sectors like education, healthcare, and government. Similarly, Charon demonstrates advanced APT-like capabilities, such as DLL sideloading and process injection, alongside network-aware behaviors to maximize impact, particularly in the Middle East’s critical infrastructure sectors. Dire Wolf, emerging in May 2025, focuses heavily on its disruptive tactics—disabling system defenses, deleting shadow copies, and erasing event logs—to make recovery nearly impossible while encrypting files with ChaCha20 and Curve25519 encryption. These emulations are intended to enable security teams to identify vulnerabilities, validate detection controls, and adapt their defenses against these targeted, financially motivated threats, with AttackIQ’s platform delivering continuous, real-world testing to elevate organizational resilience.
Risks Involved
The introduction of AttackIQ’s Ransom Tales initiative exemplifies a sophisticated approach to tackling the evolving cyber threat landscape, particularly the pervasive and destructive ransomware families like Rhysida, Charon, and Dire Wolf. These emulations simulate the tactics, techniques, and procedures (TTPs) used by adversaries, such as initial access via phishing and remote services, lateral movement using commodity tools, and complex deployment methods like DLL sideloading and process injection, often coupled with anti-detection measures. Their impact is significant: ransomware strains employ double extortion models—encrypting files while exfiltrating data—to maximize pressure on victims, disrupting critical sectors such as healthcare, government, and manufacturing. Moreover, they disable security defenses, delete backup systems, and erase logs, making detection and recovery extremely challenging. Validating security controls against these behaviors enables organizations to identify vulnerabilities, improve detection and prevention pipelines, and bolster resilience, ultimately reducing the risk of costly data breaches, operational downtime, and reputation damage in an increasingly hostile cyber environment.
Possible Actions
Ensuring swift remediation for "Ransom Tales: Volume IV – Emulating Rhysida, Charon and Dire Wolf Ransomware" is critical to minimize damage, prevent data loss, and restore normal operations. Rapid action can significantly reduce financial costs and safeguard sensitive information from malicious exploitation.
Preventive Measures
- Regular backups
- Security patches
Detection & Identification
- Continuous monitoring
- Anomaly detection
Containment Strategies
- Isolate affected systems
- Disable infected accounts
Eradication Efforts
- Remove malicious files
- Terminate malicious processes
Recovery Processes
- Restore from backups
- Verify system integrity
Follow-up Actions
- Conduct security audits
- Update incident response plans
Explore More Security Insights
Explore career growth and education via Careers & Learning, or dive into Compliance essentials.
Access world-class cyber research and guidance from IEEE.
Disclaimer: The information provided may not always be accurate or up to date. Please do your own research, as the cybersecurity landscape evolves rapidly. Intended for secondary references purposes only.
Cyberattacks-V1