Summary Points
-
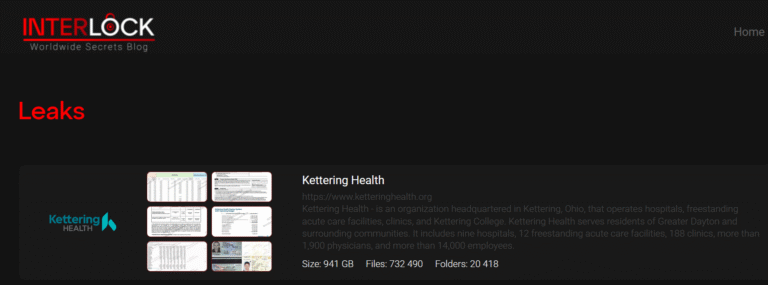
Data Breach Impact: The Interlock ransomware gang claims to have stolen 941 GB of sensitive data from Kettering Health, including files like ID cards and financial reports.
-
Cyberattack Response: Following a significant system outage caused by the cyberattack, Kettering Health managed to restore patient services and successfully launched its Epic electronic health record system.
-
Ransom Payment Denied: Kettering Health did not comply with the extortion demands from Interlock, which resulted in the gang publishing the stolen data on their leak site.
- Enhanced Security Measures: In response to the attack, Kettering Health has eradicated the threat actors’ tools, patched systems, and improved its security protocols to prevent future incidents.
Underlying Problem
In a significant cybersecurity incident, the Interlock ransomware group claimed to have stolen an immense 941 GB of sensitive data from Kettering Health, a non-profit healthcare network in Ohio, which was left reeling from a recent cyberattack. This assault led the organization to temporarily suspend patient procedures as systems crucial for patient care, including its call center operations, became compromised. However, despite the initial disruptions, Kettering Health subsequently managed to restore key services and even reinforced its technological backbone with a new launch of its Epic electronic health record system, facilitating improved patient management.
The attack occurred on May 20, 2025, and is believed to have been executed by the Interlock group, which emphasized its role by leaking the stolen data on a Tor site. While Kettering Health has not disclosed specific details regarding the nature of the attack or whether a ransom was demanded or paid, it confirmed its response involved eradicating the attackers’ presence and fortifying security protocols to thwart future breaches. The healthcare provider assured stakeholders of the integrity and security of its systems amidst increasing scrutiny, as Interlock is linked to approximately 40 prior attacks targeting various entities, posing a growing risk in the cybersecurity landscape.
Critical Concerns
The recent cyberattack on Kettering Health by the Interlock ransomware gang, which led to the exfiltration of 941 GB of sensitive data, poses significant risks to other businesses, users, and organizations by creating a ripple effect of potential vulnerabilities in interconnected systems. As cybercriminals increasingly target healthcare and other critical sectors, the exposure of patient data—such as ID cards and financial information—raises severe concerns about identity theft and fraud, potentially jeopardizing not only patient trust but also affecting insurance companies, affiliated providers, and third-party vendors reliant on secure data exchanges. Moreover, organizations that share networks or data with Kettering Health could find themselves inadvertently drawn into similar attacks, amplifying the threat landscape. This incident underscores the urgent need for robust cybersecurity measures across all sectors, as the fallout from such breaches can erode customer confidence and engender substantial financial and reputational damages, fostering an environment of heightened distrust and regulatory scrutiny.
Possible Remediation Steps
In an era where data breaches proliferate, the timely remediation of compromised information is crucial, especially in light of alarming incidents like the recent ransomware gang leak of Kettering Health data.
Mitigation Steps:
- Incident Detection: Implement real-time monitoring to identify breaches swiftly.
- Immediate Containment: Isolate affected systems to prevent further data loss.
- Data Restoration: Utilize backups to restore compromised information securely.
- Vulnerability Assessment: Conduct thorough evaluations to identify and rectify security gaps.
- Employee Training: Educate staff on recognizing suspicious activities and phishing attempts.
- Communication Plan: Notify stakeholders transparently about the breach and remedial actions taken.
NIST CSF Guidance:
NIST’s Cybersecurity Framework (CSF) emphasizes the necessity for timely response to incidents and resilience against future threats. Key Special Publications (SP) guiding this include NIST SP 800-61, which provides a roadmap for incident response planning and execution. This framework underscores the importance of preparedness, ensuring that organizations can mitigate risks effectively and restore services expediently following a breach.
Stay Ahead in Cybersecurity
Explore career growth and education via Careers & Learning, or dive into Compliance essentials.
Understand foundational security frameworks via NIST CSF on Wikipedia.
Disclaimer: The information provided may not always be accurate or up to date. Please do your own research, as the cybersecurity landscape evolves rapidly. Intended for secondary references purposes only.
Cyberattacks-V1