Essential Insights
-
Corporate Downsizing and Security Strain: Major companies are reducing their workforces, leaving CISOs with fewer resources while the frequency of security incidents, particularly involving compromised credentials, rises dramatically.
-
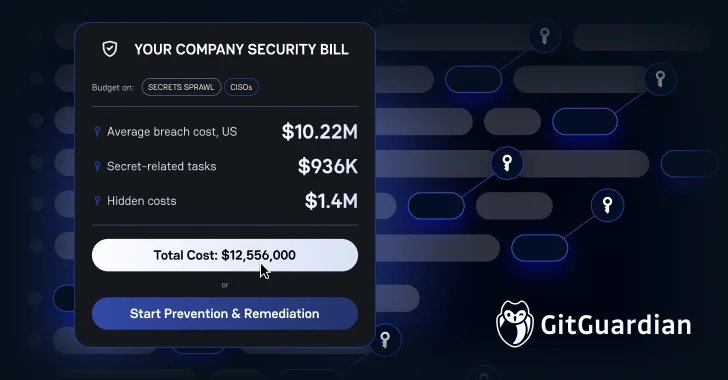
Credential Breach Costs Escalate: 86% of breaches involve stolen credentials, costing U.S. organizations over $10 million on average—with hidden management costs adding up to $1.4 million annually on manual secret handling.
-
Complexity of Secret Management: Leaner teams face longer remediation times and complexities in managing secrets across multiple platforms, leading to potential cascading security failures, as exemplified by the s1ngularity attack.
- Need for Efficient Remediation Solutions: Modern security platforms must prioritize precision in secret management, offering proactive detection, clear ownership, and efficient integrations to reduce remediation times from weeks to hours.
Incident Response in a Scarce Resource Environment
In today’s fast-paced digital landscape, Chief Information Security Officers (CISOs) face unprecedented challenges. As major corporations shrink their workforces, security teams find themselves stretched thin. This trend forces CISOs to rethink incident remediation strategies. Leaner teams may claim efficiency, yet the rise in cyber incidents highlighted by IBM research exposes a critical vulnerability. Nearly 86% of breaches now involve compromised credentials, and the cost of managing these incidents has skyrocketed. For instance, organizations waste approximately $1.4 million annually addressing hardcoded secrets. Moreover, incidents like the Canva breach illustrate how downtime can cripple operations, diverting valuable resources from core business functions.
The ramifications of these trends extend beyond immediate costs. With average incident containment times reaching 292 days, the stakes have never been higher. Each security breach not only impacts financial resources but also strains overwhelmed security teams. Consequently, many CISOs must shift from reactive to proactive remediation approaches to mitigate escalating threats effectively.
Adopting a Proactive Mindset
A strategic pivot towards more innovative remediation frameworks can empower security organizations. Traditional detection methods no longer suffice; they often create noise that burdens already hardworking teams. Effective solutions now focus on context. By understanding how and where secrets are used within the organization, teams can remediate issues more efficiently. This transformative approach prioritizes critical details, enhancing response speed from weeks to mere hours.
Modern security platforms emphasize proactive detection, assign clear ownership of secrets, and integrate smoothly into existing workflows. These advancements significantly reduce administrative burdens on developers and analysts alike. As companies strive to do more with less, adopting these smart remediation strategies provides a pathway to maintaining robust security postures. Embracing a proactive mindset equips CISOs to navigate an increasingly complex and resource-constrained landscape, ultimately contributing to broader organizational success.
Discover More Technology Insights
Explore the future of technology with our detailed insights on Artificial Intelligence.
Explore past and present digital transformations on the Internet Archive.
DataProtection-V1