Essential Insights
-
Vulnerability Overview: Two medium-severity vulnerabilities in Supermicro BMC firmware (CVE-2025-7937, CVE-2025-6198) allow attackers to bypass cryptographic signature checks, enabling the installation of malicious firmware.
-
Exploitation Mechanism: Attackers can exploit these vulnerabilities by redirecting firmware update processes to fake tables in unsigned regions, thus compromising the integrity of the BMC system and main server OS.
-
Ineffectiveness of Previous Fixes: The discovered vulnerabilities reveal inadequacies in prior fix efforts for related issues (CVE-2024-10237), allowing potential manipulation of firmware validation processes.
- Security Recommendations: Experts advise against reusing signing keys across products and recommend key rotation to mitigate risks of widespread exploitation following key leaks, enhancing overall firmware security.
New Vulnerabilities in Supermicro BMC Firmware
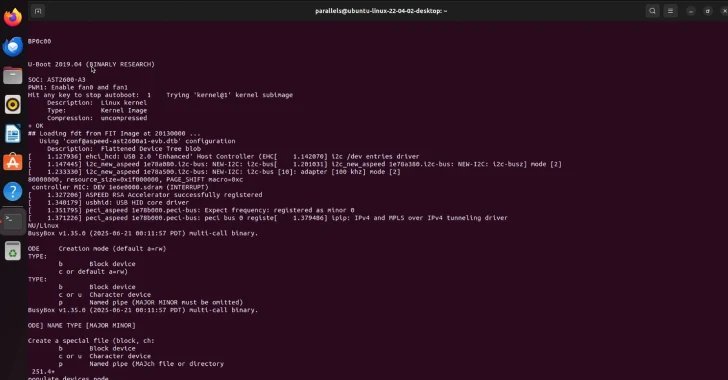
Cybersecurity researchers recently identified two significant vulnerabilities in Supermicro Baseboard Management Controller (BMC) firmware. These flaws allow attackers to bypass essential security protocols and upload malicious firmware. Particularly, the vulnerabilities exploit improper verification of cryptographic signatures. The first vulnerability, CVE-2025-7937, enables a crafted firmware image to evade the Root of Trust (RoT) verification. Similarly, CVE-2025-6198 allows attackers to bypass the Signing Table verification process.
The implications are grave. Both vulnerabilities pose medium severity risks, with CVSS scores of 6.6 and 6.4, respectively. As a result, attackers could manipulate the firmware update process. They might redirect the program to a counterfeit signing table or a fake “fwmap” table, ultimately gaining control over both the BMC system and the host operating system.
Addressing Security Flaws and Best Practices
The findings highlight critical weaknesses in the firmware validation process. Researchers from Binarly, who reported these vulnerabilities, noted that the design of the firmware verification process is not foolproof. They emphasized that malicious actors could modify key elements of the firmware update without triggering alerts. This situation raises serious concerns about the efficacy of existing security measures.
Experts urge manufacturers to adopt better practices, such as regularly updating cryptographic keys and fortifying firmware validation. They underscore that relying on a single signing key risks widespread vulnerabilities across devices. Failure to rectify these issues could lead to far-reaching consequences in the realm of cybersecurity, affecting countless systems reliant on Supermicro’s technology. Thus, addressing these flaws proves crucial for enhancing overall firmware security.
Discover More Technology Insights
Learn how the Internet of Things (IoT) is transforming everyday life.
Stay inspired by the vast knowledge available on Wikipedia.
DataProtection-V1