Summary Points
-
Security Vulnerability in Cursor: A significant flaw in the AI-powered code editor Cursor allows attackers to execute arbitrary code by exploiting a default setting that disables "Workspace Trust," enabling malicious tasks to run upon opening a project.
-
Risks of Malicious Code Execution: Opening compromised repositories can lead to severe outcomes, such as leaking sensitive information, modifying files, or allowing broader system compromises, significantly threatening Cursor users’ security.
-
Prompt Injection Threats: Emerging prompt injection attacks pose systemic risks to AI-powered coding tools, such as Claude Code, enabling malicious actors to embed harmful instructions and bypass security measures, even tricking AI into running dangerous code.
- Need for Enhanced Security Practices: Users are advised to enable security features like Workspace Trust, review code in safer environments, and adopt vigilant monitoring practices to mitigate these risks amid evolving attack strategies in AI-driven development tools.
Cursor AI Editor Vulnerability Uncovered
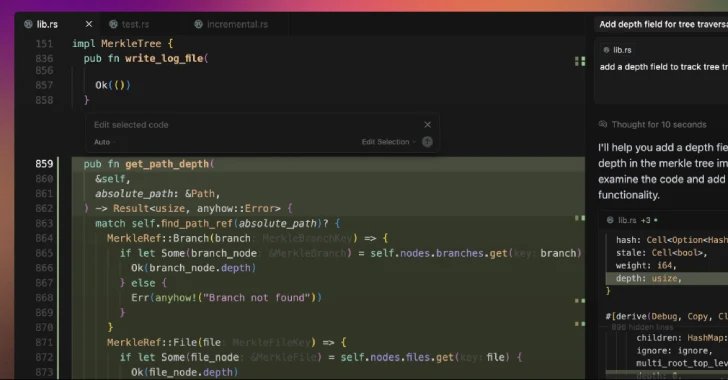
A significant security flaw has come to light in the Cursor AI code editor. This vulnerability allows malicious repositories to execute code silently when opened by unsuspecting users. The issue arises because Cursor ships with a critical security feature, Workspace Trust, disabled by default. Consequently, when users open a project folder, specific tasks can auto-execute. Researchers have emphasized that a hidden malicious script in the project can turn a routine action into a dangerous scenario. Attackers can leverage this misconfiguration to compromise users’ machines, exposing sensitive information and facilitating larger attacks.
To counteract this risk, users should enable Workspace Trust in Cursor. Additionally, they should open untrusted repositories with caution, preferably using alternative code editors. An audit of repositories before opening them within Cursor can further mitigate risks. Cybersecurity experts warn of rising threats from supply chain attacks, highlighting the growing importance of robust security measures in software development environments.
Wider Implications for AI Code Tools
The vulnerability in Cursor is part of a broader issue affecting various AI-powered coding tools. As these technologies evolve, they face both new and traditional security risks, including prompt injections that can lead to improper code execution. Recent reports demonstrate how these vulnerabilities can inadvertently expose developers to potential hazards, enabling them to push unsafe code into production.
Security experts have stressed the need for vigilance as new threats emerge, including SQL injection and authentication bypass vulnerabilities. They emphasize that while innovative tools enhance development speed, foundational security protocols must remain a priority. To safeguard the integrity of software development processes, organizations must adopt a proactive approach to security. By prioritizing protection over convenience, the industry can ensure a safer coding landscape for all.
Discover More Technology Insights
Stay informed on the revolutionary breakthroughs in Quantum Computing research.
Discover archived knowledge and digital history on the Internet Archive.
DataProtection-V1