Summary Points
-
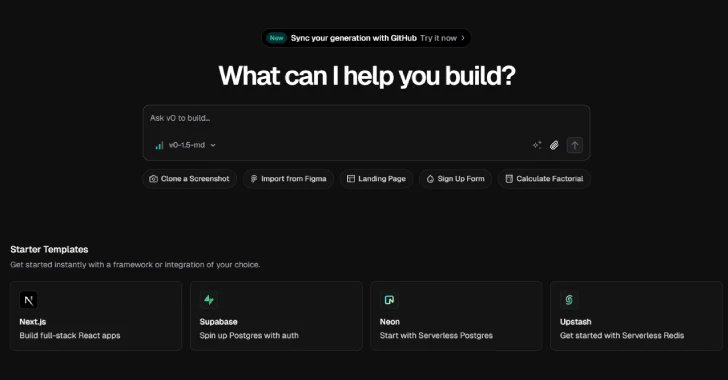
Weaponization of AI: Threat actors are using Vercel’s generative AI tool, v0, to easily create convincing phishing sites, showcasing a new level of sophistication in cybercrime.
-
Low Barrier for Entry: Unlike traditional phishing kits, v0 allows even low-skilled attackers to generate fake login pages using simple text prompts, drastically increasing the speed and scale of phishing operations.
-
Infrastructure Exploitation: Scammers are hosting impersonated company resources on Vercel’s infrastructure to exploit trust and evade detection, highlighting vulnerabilities in legitimate platforms.
- Rise of Uncensored LLMs: Cybercriminals are increasingly utilizing uncensored large language models, such as WhiteRabbitNeo, designed for illicit purposes, indicating a broader trend of AI-enabled phishing technologies.
Problem Explained
As of July 2, 2025, a troubling escalation in the realm of cybercrime has been documented, centering around the exploitation of Vercel’s generative AI tool, v0. This platform allows users to create landing pages via natural language prompts, but it has now been hijacked by unidentified threat actors. They are using v0 to fabricate convincing imitation sign-in pages for various brands, a tactic recently reported by Okta Threat Intelligence researchers Houssem Eddine Bordjiba and Paula De la Hoz. These criminal entities have demonstrated a remarkable capacity for generating functional phishing sites from simple text prompts, thereby lowering the technical barrier to entry for aspiring cybercriminals.
The ramifications are profound, as this shift signifies a transformation in phishing dynamics, with attackers now able to deploy high-quality, deceptive pages with unprecedented speed and minimal effort. Vercel has since intervened by blocking access to these fraudulent sites, yet the underlying infrastructure for these operations, including the use of impersonated company logos hosted on Vercel’s platform, highlights the exploitation of trust in legitimate services by malicious actors. Furthermore, the rise of uncensored large language models, such as WhiteRabbitNeo, fuels this trend, providing cybercriminals with tools explicitly designed for illicit activities. The combination of generative AI and uncensored models is creating a new landscape in which social engineering attacks proliferate, evolving from mere tricks into expansive, automated deception networks.
Risk Summary
The emergence of generative AI tools, such as Vercel’s v0, in the hands of malicious actors poses a significant risk not only to individual businesses but also to the wider digital ecosystem. As these threat actors exploit AI to create highly convincing phishing sites with unprecedented ease, the likelihood of user and organizational compromise skyrockets. This will result in a cascading effect—wherein compromised accounts lead to data breaches, financial losses, and severely damage reputations across various sectors. Furthermore, as small-scale scams evolve into large-scale automated attacks, vulnerabilities can affect multiple interconnected organizations, leading to widespread distrust in digital platforms and eroding user confidence. Consequently, businesses must prioritize cybersecurity measures and proactive threat monitoring to shield themselves and their customers from these evolving threats.
Possible Remediation Steps
In our increasingly digital landscape, the urgency of timely remediation cannot be overstated, particularly in the context of Vercel’s v0 AI tool being exploited by cybercriminals to generate fake login pages en masse.
Mitigation Steps:
- User Education: Educate users on recognizing phishing attempts.
- Multi-Factor Authentication (MFA): Implement MFA to enhance security.
- Monitoring Systems: Establish 24/7 monitoring for suspicious activities.
- Incident Response Plan: Develop and regularly update an incident response strategy.
- Regular Updates: Ensure Vercel tools and dependencies are consistently updated.
NIST CSF Guidance:
The NIST Cybersecurity Framework (CSF) emphasizes the importance of identifying, protecting, detecting, responding, and recovering from cyber incidents. Specifically, refer to NIST SP 800-53 for detailed security and privacy controls, which can guide organizations in fortifying their defenses against such threats.
Advance Your Cyber Knowledge
Discover cutting-edge developments in Emerging Tech and industry Insights.
Understand foundational security frameworks via NIST CSF on Wikipedia.
Disclaimer: The information provided may not always be accurate or up to date. Please do your own research, as the cybersecurity landscape evolves rapidly. Intended for secondary references purposes only.
Cyberattacks-V1