Summary Points
-
Vulnerability Discovery: A security firm found nearly 400 critical human-machine interfaces (HMIs) in U.S. water utilities exposed to the internet, with 40 devices fully unauthenticated, allowing anyone to control them.
-
Rapid Remediation: Following intervention from the security firm and the EPA, utilities secured their systems swiftly, reducing online unauthenticated access to fewer than 6% by May, with nearly 60% fixing issues within weeks.
-
Sector’s Cybersecurity Challenges: The water sector, facing significant cyber threats from state-linked groups and ransomware, remains particularly vulnerable due to limited funding and expertise for cybersecurity defenses.
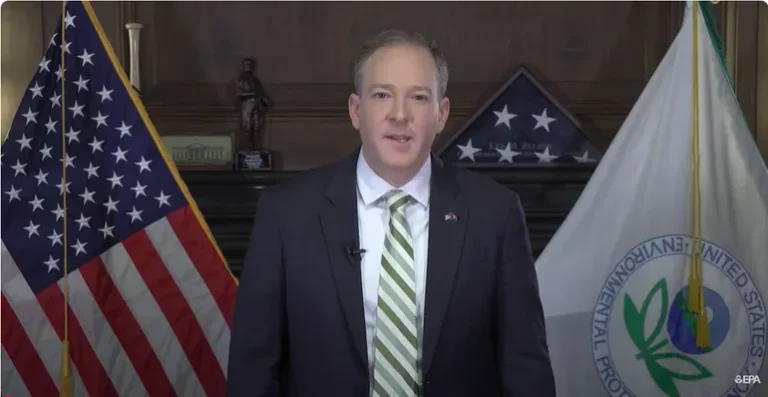
- Federal Awareness and Action: In response to the vulnerabilities, the EPA and the HMI device manufacturer implemented changes like multifactor authentication, highlighting the increasing threat of cyberattacks on critical infrastructure.
Addressing Vulnerabilities
Recent findings reveal significant security flaws in U.S. water utilities. Researchers discovered that nearly 400 industrial control systems, vital for managing water facilities, were accessible online. Alarmingly, 40 of these systems were fully controllable by anyone with internet access. This situation poses an immediate threat to public safety.
After the discovery, many water utilities took swift action. Collaborating with experts from a security firm, agencies like the Environmental Protection Agency played a crucial role. By May, fewer than 6% of the vulnerable systems remained exposed. Nearly a quarter of the utilities resolved issues within just nine days, showcasing the sector’s responsiveness.
Building Resilience
The water sector has historically faced numerous cyber threats. Attackers often target it due to its insufficient funding and expertise in cybersecurity. The recent report highlights ongoing vulnerabilities affecting millions of Americans. Approximately 26 million individuals depend on utilities with severe security risks.
In response, manufacturers are implementing protections like multifactor authentication. Action from the EPA indicates a growing awareness of these critical vulnerabilities. As water utilities enhance their security, they also set a precedent for infrastructure resilience. Such measures contribute to public safety and strengthen trust in essential services.
Continue Your Tech Journey
Learn how the Internet of Things (IoT) is transforming everyday life.
Stay inspired by the vast knowledge available on Wikipedia.
Cybersecurity-V1