Fast Facts
- Traditional security testing is inadequate for AI systems; specialized AI penetration testing addresses unique threats like prompt injection and data poisoning to ensure security and trustworthiness.
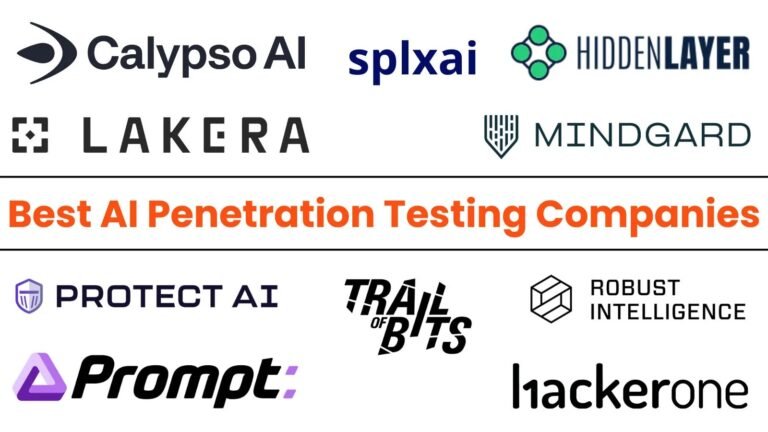
- Leading companies such as CalypsoAI, Mindgard, and Lakera provide automated, comprehensive platforms tailored for AI vulnerabilities, integrating into development processes to proactively secure AI models.
- Runtime monitoring and red teaming by firms like HiddenLayer and Robust Intelligence are crucial for defending live AI systems against emerging adversarial attacks, especially in sensitive sectors.
- The industry emphasizes a combination of expert-led, research-driven testing and scalable, automated solutions, vital for organizations to safeguard their AI assets and maintain compliance amid evolving threats.
The Issue
In 2025, the landscape of AI security has evolved dramatically, emphasizing the critical need for AI penetration testing to safeguard against emerging threats such as adversarial attacks, prompt injections, and data poisoning that traditional security measures cannot detect. These specialized testing services are crucial for organizations deploying AI in sensitive areas like finance, healthcare, and enterprise operations, aiming to prevent vulnerabilities that could lead to data breaches, reputational damage, or regulatory fines. Leading companies such as CalypsoAI, Mindgard, and Lakera have developed purpose-built platforms capable of continuous, automated testing across the entire AI lifecycle, integrating security measures seamlessly into development processes and monitoring models in real-time. Meanwhile, established security firms like HackerOne and Trail of Bits leverage their extensive expertise and community networks to provide comprehensive, scalable solutions tailored to the complex, unique threats posed by AI systems, offering organizations an essential defense against the rapidly evolving cyber threat landscape targeting AI infrastructures.
Risks Involved
As AI increasingly becomes integral to business processes, its unique vulnerabilities—such as prompt injection, data poisoning, and adversarial attacks—have created a specialized attack surface that traditional security measures cannot adequately address. AI-specific penetration testing has emerged as a crucial defense mechanism, employing techniques like adversarial ML, red-teaming for Large Language Models (LLMs), and continuous lifecycle security integration to proactively identify and mitigate threats that can corrupt AI behavior, leak sensitive data, or compromise trustworthiness. Leading providers—such as CalypsoAI, HiddenLayer, and Lakera—offer advanced, automated platforms capable of real-world attack simulation, runtime threat detection, and comprehensive coverage from development to deployment, while established firms like HackerOne and Trail of Bits leverage extensive research and community intelligence for scalable, expert-led assessments. As AI’s role expands, deploying these specialized testing solutions is essential for safeguarding organizational assets, ensuring regulatory compliance, and maintaining operational integrity against an evolving landscape of cyber threats uniquely tailored to AI systems.
Possible Action Plan
Prompt detection and prompt remediation are critical in maintaining the integrity and trustworthiness of AI systems, especially as they become more integral to cybersecurity defenses. Addressing vulnerabilities early not only minimizes potential damage but also ensures continuous compliance with evolving standards and mitigates the risk of exploitation.
Mitigation Steps
- Regular Vulnerability Scans
- Immediate Patch Deployment
- Strengthening Access Controls
- Conducting Penetration Tests
- Updating Security Protocols
- Employee Security Training
Advance Your Cyber Knowledge
Stay informed on the latest Threat Intelligence and Cyberattacks.
Understand foundational security frameworks via NIST CSF on Wikipedia.
Disclaimer: The information provided may not always be accurate or up to date. Please do your own research, as the cybersecurity landscape evolves rapidly. Intended for secondary references purposes only.
Cyberattacks-V1