Essential Insights
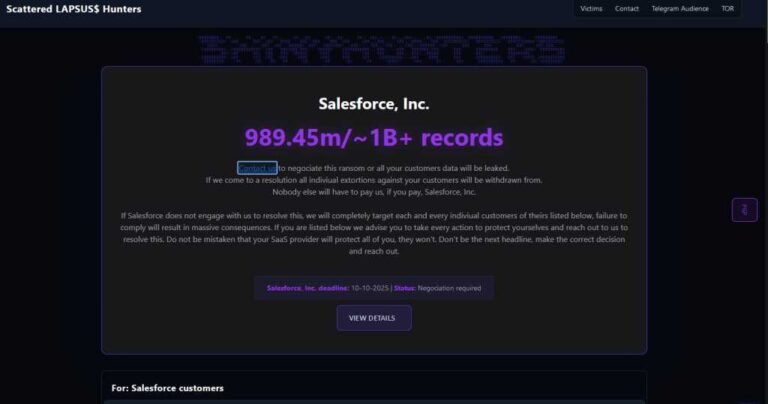
- A threat was issued by the Scattered Lapsus$ Hunters, a coalition of ransomware groups, to leak one billion records stolen from Salesforce, targeting major global companies like Disney and Toyota.
- The hackers demanded a ransom payment by October 10 to prevent the release of sensitive customer data.
- The threat included a warning of widespread targeting of Salesforce’s individual customers if demands were not met.
- The incident highlights ongoing risks and potential catastrophic data breaches involving major corporations and organized cybercrime groups.
The Issue
Recently, a cybercriminal alliance called Scattered Lapsus$ Hunters, involving notorious groups like ShinyHunters, Scattered Spider, and LAPSUS$, issued a chilling threat on the BreachForums extortion site. They claimed to have stolen and threatened to leak a staggering one billion records from Salesforce, affecting 39 major corporations including Disney, Toyota, McDonald’s, and IKEA. The hackers demanded that Salesforce pay a ransom by October 10th at 11:59 p.m. EST, warning that failure to comply would result in the release of sensitive customer data and severe consequences for the affected companies and their users.
This threatening message indicates that the attackers are targeting Salesforce’s vast customer base, suggesting they possess extensive, highly valuable data. The motivation stems from a common ransomware tactic, where criminals threaten to release stolen information unless their ransom demands are met. The incident was publicly reported by cybersecurity sources monitoring cybercrime forums, warning of the serious breach and the dangerous implications for corporate data security, with the hackers asserting their readiness to escalate their attack if their demands aren’t satisfied.
Risks Involved
The recent cyber attack involving the threat to leak one billion records from Salesforce highlights the severe risks posed by organized cybercriminal alliances like the LAPSUS$, Scattered Spider, and ShinyHunters. These groups leverage ransomware, extortion, and data breaches to threaten global corporations, jeopardizing customer privacy, damaging brand reputation, and causing financial loss. Their tactics include using both the dark web and accessible internet channels to demand ransom payments, warning of widespread data exposure and operational disruption if demands are unmet. Such incidents underscore how malicious actors target critical business infrastructure, amplifying the potential for massive data leaks, legal liabilities, and erosion of public trust—an urgent call for organizations to bolster cybersecurity defenses, enforce incident response plans, and remain vigilant against evolving cyber threats.
Possible Action Plan
Prompt action in the face of the FBI seizing BreachForums servers is critical to minimizing the fallout and preventing further damage, especially as a deadline for a confidential Salesforce data release draws near. Addressing this swiftly ensures that organizations contain vulnerabilities, mitigate data breaches, and maintain trust among stakeholders.
Immediate Containment
Isolate affected servers to prevent data exfiltration or further intrusion.
Legal Coordination
Engage legal counsel to understand regulatory obligations and to coordinate with law enforcement efforts.
Forensic Investigation
Conduct comprehensive digital forensics to ascertain the breach scope and gather evidence for potential legal proceedings.
Patch and Update
Apply necessary security patches, update software, and strengthen defenses to prevent similar future breaches.
Communication Strategy
Inform relevant stakeholders, customers, and regulators transparently to uphold credibility and manage expectations.
Data Preservation
Secure and preserve critical logs and data for analysis and potential prosecution.
Enhanced Monitoring
Increase monitoring and intrusion detection to rapidly identify any ongoing malicious activity.
User Certification
Notify and educate users on potential risks, including password resets and credential updates.
Long-term Security Review
Implement comprehensive security audits and revise policies to bolster resilience against future threats.
Explore More Security Insights
Stay informed on the latest Threat Intelligence and Cyberattacks.
Access world-class cyber research and guidance from IEEE.
Disclaimer: The information provided may not always be accurate or up to date. Please do your own research, as the cybersecurity landscape evolves rapidly. Intended for secondary references purposes only.
Cyberattacks-V1