Quick Takeaways
- Microsoft has revealed a critical zero-day (CVE-2025-59230) in Windows’ RasMan service, allowing low-privilege users to escalate to SYSTEM level and potentially take full control of affected systems.
- The vulnerability, affecting multiple Windows versions (including Windows 10, 11, and Server editions from 2019 onwards), is actively exploited in the wild with proof-of-exploit evidence observed.
- Exploiting RasMan involves manipulating service files via registry edits or DLL injections, facilitating privilege escalation and further lateral movement post-initial breach.
- With a high severity score of 7.8, Microsoft urges immediate patching through October 2025 updates, as unpatched systems face heightened risks from advanced threat actors including nation-states and ransomware groups.
What’s the Problem?
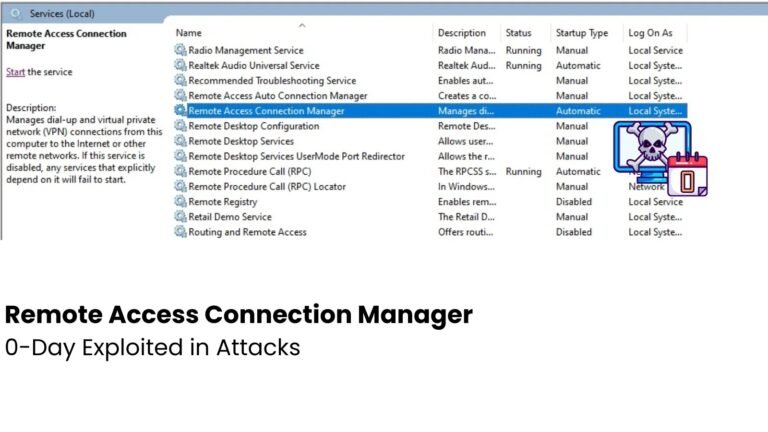
Microsoft has confirmed that a dangerous vulnerability, identified as CVE-2025-59230, is actively being exploited in Windows’ Remote Access Connection Manager (RasMan), a crucial component responsible for remote connectivity services like VPNs. This flaw stems from weak access controls within RasMan, allowing malicious actors with only basic local access and low privileges to escalate their privileges to the highest level—SYSTEM—potentially compromising entire systems. The vulnerability’s high severity score of 7.8 underscores its potential for widespread damage, especially since threat actors are already exploiting it in real-world attacks, although detailed victim information remains private. Cybercriminals or nation-state hackers can manipulate RasMan’s configuration or inject malicious code via registry hacks or DLL injections, enabling them to take full control of affected machines, often as a step in larger attack chains involving phishing or exploitation of unpatched software.
This security flaw impacts multiple Windows versions, including Windows 10 (from version 1809 onward), Windows 11, and Windows Server editions from 2019 through 2025. Microsoft’s urgent advice is to apply the latest October 2025 patches immediately, as the vulnerability not only facilitates system takeovers but also leaves unpatched devices highly vulnerable to further exploitation by sophisticated threat actors, including ransomware groups and state-sponsored hackers. With proof-of-exploit activity already detected in the wild, the urgency to mitigate this flaw has never been greater, emphasizing the necessity for organizations and users to patch promptly to prevent potentially catastrophic breaches.
Risk Summary
Microsoft has revealed a critical zero-day vulnerability (CVE-2025-59230) in the Windows Remote Access Connection Manager (RasMan) service, which allows malicious actors to escalate privileges from low-level user accounts to SYSTEM-level control, potentially leading to total system compromise. Exploited through weak access controls in a core component responsible for remote connections like VPNs, this flaw affects multiple Windows versions, including Windows 10, 11, and Server editions, and has already been targeted in active attacks. With a high severity CVSS score of 7.8, the vulnerability permits local attackers, without user interaction, to manipulate service configurations and inject malicious code—using methods like registry modification or DLL injection—thus enabling full system takeover. The threat is heightened by the ease of exploitation and its presence in the wild, especially since unpatched systems are vulnerable to nation-state assaults and ransomware, underscoring the urgent need for immediate patching to prevent widespread damage.
Possible Actions
Ensuring prompt remediation of the Windows Remote Access Connection Manager 0-Day Vulnerability is crucial in safeguarding critical systems and preventing widespread exploitation. If left unaddressed, attackers can leverage this vulnerability to gain unauthorized access and control over affected devices, leading to data breaches, system disruptions, and potential infrastructure compromise.
Mitigation Strategies:
- Apply Security Patches
- Disable Affected Services
- Implement Network Segmentation
- Enable Firewall Restrictions
- Monitor Network Traffic
- Conduct Vulnerability Scans
- Update Antivirus Signatures
Stay Ahead in Cybersecurity
Stay informed on the latest Threat Intelligence and Cyberattacks.
Access world-class cyber research and guidance from IEEE.
Disclaimer: The information provided may not always be accurate or up to date. Please do your own research, as the cybersecurity landscape evolves rapidly. Intended for secondary references purposes only.
Cyberattacks-V1