Quick Takeaways
- A Vietnamese-linked operation, known as AccountDumpling, uses Google AppSheet as a "phishing relay" to target Facebook accounts, compromising around 30,000 users.
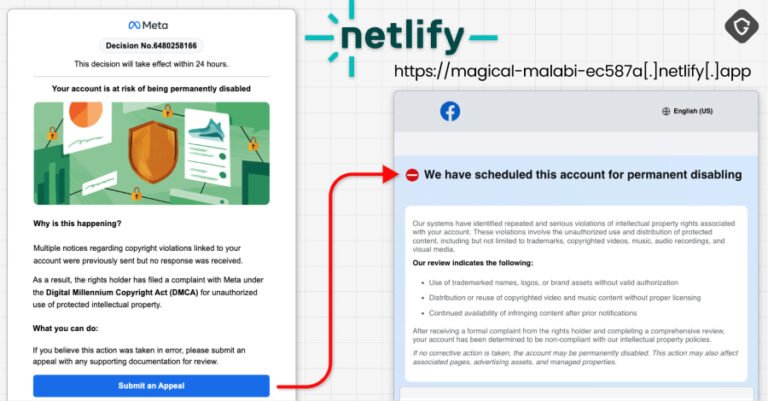
- The attack starts with spoofed emails claiming to be from Meta Support, prompting victims to a fake webpage designed to steal login credentials.
- The campaign employs various scare tactics—like account disablement and job offers—and hosts fake help pages and PDFs to harvest sensitive data.
- Evidence links the operation to a Vietnamese digital marketing business ("phamtaitan.vn"), highlighting a large, organized cybercriminal ecosystem trading stolen Facebook assets.
Phishing Campaign Uses Google AppSheet to Steal Facebook Accounts
Recently, a new type of cyberattack has emerged that targets Facebook users. Hackers from Vietnam are using a Google AppSheet platform to send deceptive emails. These emails pretend to be from Meta Support, warning users to act quickly or lose access to their accounts forever. The emails contain a false sense of urgency, pushing victims to click on fake links. Once clicked, victims land on fake web pages designed to steal their login details and personal information. This method cleverly bypasses spam filters because the emails come from a legitimate-looking AppSheet address. In just a few weeks, around 30,000 Facebook accounts have been compromised through this campaign.
The attackers have created a sophisticated operation. They set up real-time control panels, use advanced ways to avoid detection, and keep evolving their tactics. This ongoing criminal effort is not just about stealing accounts; it also involves selling these accounts on underground markets. The stolen accounts are most often sold for monetary gain. This campaign shows how cybercriminals continually adapt, using trusted platforms creatively to carry out illegal activities. It highlights a broader problem of cyber threats evolving rapidly and finding new ways to exploit popular social media platforms.
Fake Emails and Phishing Tactics Fueling the Attack
The attack begins with phishing emails that look very convincing. They claim to be from Meta Support, warning about account issues like disablement or verification problems. These emails are sent from a Google AppSheet address, making them seem legitimate and helping them get past spam filters. The message then directs users to fake websites hosted on platforms like Netlify and Vercel. These sites mimic official Facebook pages, asking for personal data such as birth dates, phone numbers, and government IDs. Some of these fake pages include CAPTCHA checks before collecting user information.
Furthermore, the hackers use a variety of tactics to tempt victims. They send PDFs that appear to contain account verification instructions, fake job offers from well-known companies, and alerts about account problems. These tricks entice users into revealing passwords, two-factor authentication codes, and browsing screenshots. Most of the victims are based in countries like the United States, Italy, Canada, India, and others. The collected data is then transferred through Telegram channels for the hackers’ benefit. Evidence from the campaign points to a large operation run by individuals using a website offering digital marketing services, revealing a complex network behind these malicious activities.
Expand Your Tech Knowledge
Explore the future of technology with our detailed insights on Artificial Intelligence.
Discover archived knowledge and digital history on the Internet Archive.
DataProtection-V1