Top Highlights
-
Targeted Attacks: Sophisticated Chinese government-linked hackers are breaching technology firms and legal services, utilizing stealthy malware to steal sensitive data, including source code of enterprise technologies.
-
Ongoing Campaign: The group, primarily identified as UNC5221, is actively conducting operations that mirror previous high-profile campaigns, like the SolarWinds incident, focusing on both major vendors and their customers.
-
Malware Signature: The attackers deploy a backdoor malware called Brickstorm that circumvents typical detection methods, leading to an alarmingly long average dwell time of 393 days before intrusions are uncovered.
- Persistent Threat: Google emphasizes the enduring nature of this threat, predicting continued ripple effects from these breaches long into the future as evidence of compromises emerges and new victims are revealed.
Hiding in the Gaps
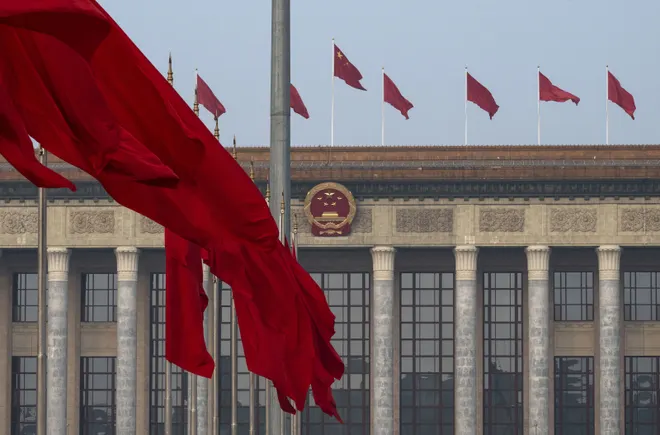
China-linked hackers target software suppliers and technology companies using stealthy malware. This sophisticated method allows them to gain access to critical data unnoticed. Recently, Google reported these hackers moved from service providers to customer networks, seeking sensitive emails and information about U.S. national security. The group behind these attacks, known as UNC5221, employs a malware backdoor named Brickstorm. This tool operates undetected on systems incapable of running standard security software, leading to unusually long detection times—averaging 393 days. Such long dwell times indicate a new level of stealth and complexity in cyber threats.
Google aims to counteract this with new tools for companies to scan their networks for traces of Brickstorm. Despite these efforts, many organizations may find evidence of past compromises or ongoing threats. Experts emphasize the need for comprehensive investigations if any signs of the malware appear. Failing to act swiftly could lead to grave consequences.
Patient Adversary, Long-Term Ripple Effects
The persistent presence of UNC5221 highlights the evolving nature of cyber warfare. Their ability to operate in a manner that avoids detection sets them apart from other adversaries. They carefully strategize to leave no recognizable pattern. This patience allows them to exploit systems over extended periods, applying threats subtly yet effectively. As companies face these challenges, they often overlook initial signs of compromise due to automated log deletions.
Consequently, the ramifications of these breaches could unfold for months or even years. The continuous threat serves as a wake-up call for organizations globally. They must adapt their cybersecurity strategies to withstand such advanced campaigns. As we navigate this digital landscape, recognizing and addressing these threats becomes critical in safeguarding not just individual companies but also national security interests.
Stay Ahead with the Latest Tech Trends
Dive deeper into the world of Cryptocurrency and its impact on global finance.
Access comprehensive resources on technology by visiting Wikipedia.
Cybersecurity-V1