Quick Takeaways
- Moltbook exposed sensitive data, including email addresses and API tokens, highlighting risks from unsecured AI agent databases.
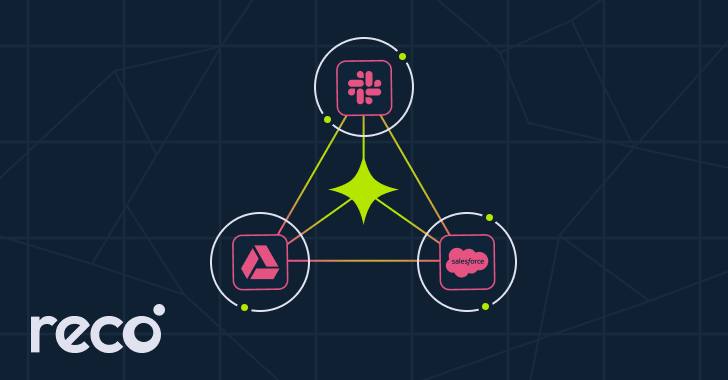
- Toxic security risks occur when AI agents or integrations bridge multiple applications via OAuth or API scopes without proper oversight.
- Traditional single-application reviews miss these complex, runtime-established trust relationships, increasing vulnerability.
- Dynamic SaaS security platforms like Reco monitor cross-application permissions continuously, identifying and mitigating toxic combinations in real-time.
How Cross-App Permissions Create Hidden Risks
In today’s digital environment, many organizations use multiple apps that work together through OAuth grants and API scopes. While each app might seem secure on its own, problems emerge when these apps connect without proper oversight. For example, an AI agent or a connector that links two services can carry permissions and credentials across platforms. These connections often go unnoticed because the existing review processes focus on individual apps, not their combined interactions. Consequently, dangerous permission overlaps can form, paving the way for security breaches. When these bridges are left unchecked, they create a toxic combination, exposing sensitive data and increasing the chance of malicious activity.
The Need for Better Oversight and Continuous Monitoring
Standard security reviews typically evaluate each app separately, which leaves gaps in the system. Scopes and permissions that look harmless on their own may become risky when combined through integrations. As these connections are created dynamically, attackers can exploit weaknesses without triggering traditional alerts. To prevent this, organizations need to shift focus from single-application reviews to continuous monitoring of the entire ecosystem. Advanced platforms, like dynamic SaaS security tools, track identities, permissions, and data flows in real time. They uncover hidden bridges and flag suspicious activity, helping organizations identify and revoke risky permissions before damage occurs. This proactive approach ensures a safer, more transparent human-digital journey in an increasingly interconnected world.
Expand Your Tech Knowledge
Dive deeper into the world of Cryptocurrency and its impact on global finance.
Access comprehensive resources on technology by visiting Wikipedia.
DataProtection-V1