Top Highlights
-
Network Identification: Ukrainian IP network FDN3 has been implicated in extensive brute-force and password spraying attacks targeting SSL VPN and RDP devices, primarily between June and July 2025.
-
Collaborative Infrastructure: FDN3 is part of a broader infrastructure involving two other Ukrainian networks (VAIZ-AS and ERISHENNYA-ASN) and a Seychelles-based system (TK-NET), creating complex interconnected hosting services to evade detection.
-
Common Host Associations: These networks are linked to bulletproof hosting operations, often associated with shell companies, and have a history of hosting similar malicious activities, including spam distribution and malware command-and-control.
- Ransomware Vulnerability: The attack techniques employed align with methods used by ransomware groups, suggesting a significant vulnerability for organizations reliant on SSL VPN and RDP assets to breaches and cyberattacks.
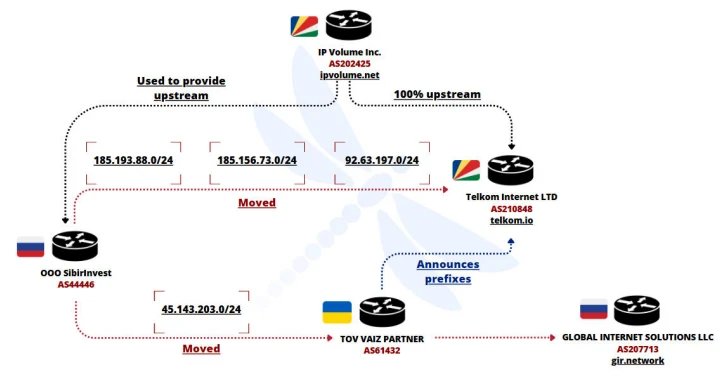
FDN3’s Alarming Cyber Campaign
Cybersecurity researchers have identified a Ukrainian network, FDN3, engaging in extensive brute-force and password spraying attacks on SSL VPN and RDP devices. This activity spanned from June to July 2025, causing significant concern among experts. Originating from the Ukraine-based autonomous system AS211736, these attacks targeted essential network infrastructure. Additionally, researchers believe FDN3 operates within a larger framework that includes two other Ukrainian networks, VAIZ-AS and ERISHENNYA-ASN, as well as a Seychelles-based system known as TK-NET. These networks often collaborate to evade detection and blocklisting, ultimately facilitating ongoing malicious operations.
Furthermore, FDN3 displays operational overlaps with previously identified networks involved in spam distribution and malware hosting. In fact, traffic from FDN3 saw a spike between July 6 and 8, indicating an unprecedented level of brute-force attempts against corporate assets. Experts note that these methods have become increasingly popular within ransomware-as-a-service groups. As FDN3 and its associated networks continue to exploit vulnerabilities in system security, the need for robust cybersecurity measures becomes more urgent. The intricate web of interconnected networks underscores a troubling trend in cybercrime, as perpetrators leverage the anonymity offered by offshore hosting services.
The Broader Implications for Cybersecurity
The alarming findings about FDN3 also highlight a systematic approach to cybercrime facilitated by offshore ISPs, such as IP Volume Inc. By allowing smaller networks to thrive through strategic peering agreements, these ISPs complicate efforts to trace malicious activities back to their source. This pattern emphasizes the challenges faced by cybersecurity professionals in combating rapidly evolving threats. Moreover, the connection to historical bulletproof hosting providers linked to Russian companies further complicates the landscape of cybercrime, as it demonstrates how interconnected and sophisticated these networks can be.
As cyberattacks continue to rise in frequency and complexity, organizations must prioritize their cybersecurity strategies. Investing in advanced security measures and adopting a proactive approach to vulnerability assessments can mitigate risks. The cyclical nature of these cyber incidents sheds light on the necessity for collaboration between businesses, law enforcement, and cybersecurity experts. In doing so, stakeholders can cultivate a more resilient digital environment, safeguarding important infrastructure and reducing the odds of future breaches.
Continue Your Tech Journey
Learn how the Internet of Things (IoT) is transforming everyday life.
Discover archived knowledge and digital history on the Internet Archive.
DataProtection-V1