Fast Facts
- Researchers discovered “DeepLoad,” a malware strain capable of stealing browser credentials and live keystrokes immediately after infection, using AI-generated code and process injection to evade detection.
- DeepLoad employs social engineering through “ClickFix” prompts, creating persistent scheduled tasks and using legitimate Windows tools to silently maintain access even after initial cleanup.
- The malware’s heavily obfuscated, AI-generated loader disguises its malicious payload, which injects into a trusted Windows process, complicating detection efforts.
- Standard cleanup methods are insufficient; organizations must audit WMI subscriptions, enable advanced logging, and change all credentials to fully remediate DeepLoad infections due to its persistent, evolving mechanisms.
Advanced Malware Uses AI to Steal Credentials and Evade Detection
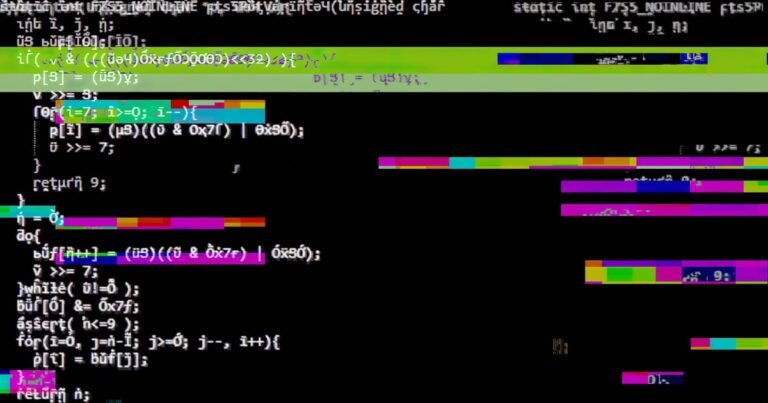
Researchers have discovered a new type of malware called DeepLoad that can quickly steal login information after infecting a network. It captures passwords stored in browsers and even records keystrokes in real time. This malware uses a standalone stealer program and a malicious browser extension to gather data. Its innovative techniques make it very hard for security tools to detect and stop. According to experts, DeepLoad likely uses AI-generated code and process injection to avoid being caught. Even if system scans find some parts of it, the malware can silently re-execute and stay active. This persistent nature allows it to continue stealing information long after initial infection.
DeepLoad Spreads and Avoids Detection Through Clever Tricks
The malware is often delivered through a social engineering attack called ClickFix. In these scams, users receive fake prompts asking them to fix supposed errors. Once triggered, the malware creates scheduled tasks to run again after rebooting the computer, making it difficult to remove. It also uses legitimate Windows tools to communicate with the attacker’s servers and download more malicious code. DeepLoad’s core code is hidden under thousands of lines of bogus data, likely created by AI, making it hard for scanners to identify. It unpacks its payload in memory, then injects it into a normal Windows process to stay hidden. The malware can spread via USB drives, copying fake installers to infect other systems. This broad approach aims to maximize its chances of stealing credentials and maintaining control over compromised machines. Standard cleanup methods are often ineffective because DeepLoad reactivates through Windows management features, requiring organizations to thoroughly review and remove these hidden triggers to fully recover.
Expand Your Tech Knowledge
Learn how the Internet of Things (IoT) is transforming everyday life.
Discover archived knowledge and digital history on the Internet Archive.
CyberRisk-V1