Summary Points
-
Recent hospital ransomware attacks, including a significant incident at the University of Mississippi Medical Center (UMMC), highlighted the urgency of cybersecurity in healthcare, coinciding with a relevant episode of HBO’s The Pitt showcasing a fictional hospital facing a cyberthreat.
-
Experts acknowledged the episode’s realism in depicting the chaos following a system shutdown—illustrating the heavy reliance of healthcare on IT—though they noted some dramatized elements, like uninterrupted patient monitoring and a simplistic closure decision by hospital leadership.
-
UMMC’s recent ransomware attack delayed patient care significantly, reflecting the increasing trend where 70% of affected healthcare facilities report disruptions due to such cyber incidents.
-
To combat ransomware, healthcare facilities should prioritize securing credentials, develop practical downtime plans for patient care, and conduct regular resilience tests through tabletop exercises to ensure well-informed decision-making during crises.
Ransomware Attacks: Art Imitates Life
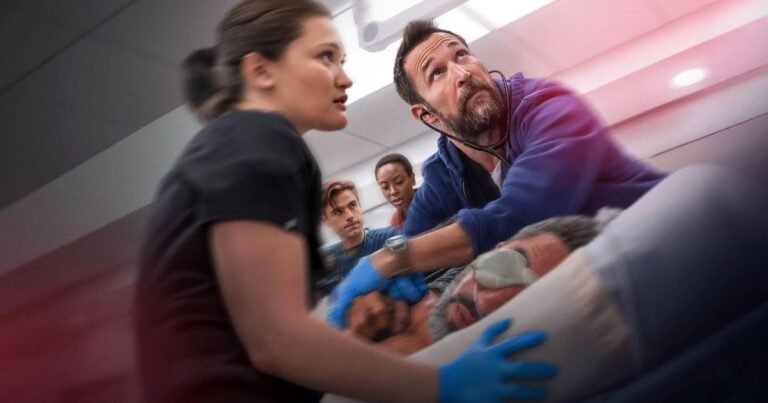
This past week highlighted the urgent issue of ransomware attacks on hospitals. A significant event unfolded in Mississippi, just as a popular HBO series, The Pitt, depicted a similar situation. On February 19, the show aired an episode focusing on a cyber threat to a fictional trauma center. The plot centered around the hospital CEO deciding to shut down IT systems to mitigate risks, mirroring real-world fears. In an unfortunate twist, on the same morning, the University of Mississippi Medical Center experienced an actual ransomware attack. Their IT infrastructure, including electronic medical records, went offline, forcing them to take drastic measures across their network of 35 clinics.
Consequently, experts are debating the accuracy of HBO’s portrayal. Some argue its representation of turmoil in healthcare facilities resonates with reality. However, they also caution that fictional narratives can oversimplify the multifaceted chaos that cyberattacks create. Experts highlighted that the episode struck an emotional chord, showing how reliant healthcare has become on technology.
Addressing the Threat: Insights and Strategies
Experts express concern about the increasing trend of disruptive ransomware attacks in healthcare. According to recent reports, approximately 70% of affected facilities have faced patient care interruptions. The urgency of addressing this issue cannot be overstated. Cybersecurity professionals stress three primary areas for hospitals to focus on: securing credentials, planning for clinical resilience, and testing their responsiveness. First, securing credentials is crucial as they often serve as gateways for attackers.
Next, hospitals must ensure that patient care remains a priority even during IT outages. Finally, testing their resilience through simulated drills enables healthcare teams to make informed decisions in high-pressure scenarios. These measures not only improve operational efficiency but also enhance patient safety. Importantly, healthcare executives are beginning to recognize the intersection between cybersecurity and patient well-being. This growing awareness marks a vital shift in how institutions approach cyber threats.
Continue Your Tech Journey
Stay informed on the revolutionary breakthroughs in Quantum Computing research.
Discover archived knowledge and digital history on the Internet Archive.
CyberRisk-V1