Quick Takeaways
-
Human Behavior Exploited: Hackers are increasingly leveraging age-old human behaviors combined with advanced technologies like deepfakes and voice cloning to breach corporate IT systems.
-
Targeting Executives: Social engineering was the primary access method in 36% of incident response cases, focusing on privileged accounts, particularly those of executives, to gain sensitive information.
-
Increased Disruption: Over half of social-engineering attacks accessed sensitive data, disrupting business functions and highlighting the heightened risk for companies and their executives.
- Evolving Tactics: As traditional methods falter due to enhanced security measures, attackers are adopting innovative social-engineering strategies, including impersonation and exploiting personal information from social media.
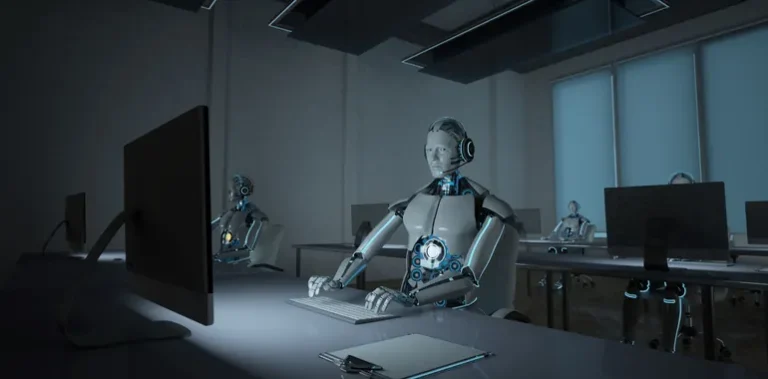
The Rise of Social Engineering
Social engineering is quickly becoming the top method for hackers to breach corporate IT systems. Traditional security measures often focus on technical flaws, yet attackers now exploit fundamental human behaviors. A recent report highlighted that 36% of successful incidents involved social engineering. This strategy allows hackers to target high-profile individuals, such as executives or government officials. By impersonating these key figures, they maximize their impact. The heightened risk stems from sophisticated tools like deepfake videos and AI voice cloning. Thus, the barrier between personal and corporate privacy continues to erode.
Moreover, hackers have used this method to access sensitive data in over half of the reported incidents. They manipulate emotions, trust, and urgency to trick employees into revealing crucial information. For example, the Co-op attack showed how impersonating an employee can lead to significant financial losses and operational disruptions. As companies tighten technical defenses, attackers pivot to more clever social-engineering tactics. This shift presents a real challenge for organizations that need to rethink their cybersecurity strategies.
Adaptation and Prevention Strategies
Companies must stay ahead of these evolving threats to protect themselves. Basic cybersecurity training that includes awareness of these tactics can fortify defenses. High-value targets, like executives, should minimize their digital footprint and limit social media sharing about personal activities. They also need to be vigilant when disseminating information to others. Using phishing-resistant multifactor authentication further strengthens security. This combination of proactive and defensive measures can significantly reduce vulnerability.
Overall, as social engineering tactics evolve, so must our strategies to combat them. The balance between innovation and security remains critical. As technology becomes more sophisticated, individuals and organizations should prioritize awareness and education. By fostering a culture of vigilance, businesses can better safeguard their operations against an unsettling rise in social engineering attacks.
Expand Your Tech Knowledge
Dive deeper into the world of Cryptocurrency and its impact on global finance.
Discover archived knowledge and digital history on the Internet Archive.