Quick Takeaways
- A critical security flaw (CVE-2026-34040) in Docker Engine allows attackers to bypass authorization plugins and gain privileged access through specially crafted HTTP requests.
- The vulnerability stems from improper handling of oversized request bodies, enabling malicious actors to create privileged containers with host system access, risking credentials and infrastructure compromise.
- Attackers, including AI agents, can exploit this flaw without special tools or privileges, using simple HTTP padding techniques to execute malicious actions like mounting host files and extracting sensitive information.
- Mitigation strategies include avoiding request body-inspecting plugins, restricting Docker API access, and running Docker in rootless mode to minimize the impact of potential exploits.
New Vulnerability Allows Attackers to Bypass Docker Authorization
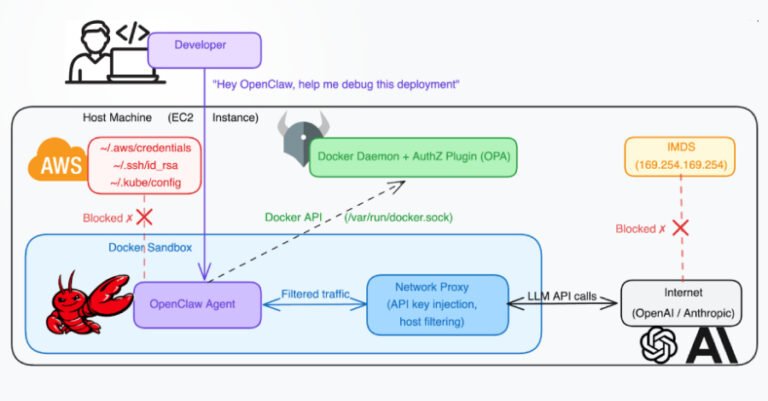
A recent security flaw in Docker Engine poses a significant threat to container security. The vulnerability, identified as CVE-2026-34040, allows attackers to sidestep authorization checks. This flaw stems from an incomplete fix of a previous, high-severity issue. When exploited, it enables malicious actors to send specially crafted API requests that skip authorization steps. As a result, they can create privileged containers with full access to the host system. Security researchers highlight that this bug mainly affects systems relying on authorization plugins that analyze request bodies for security decisions. The flaw was discovered independently by multiple security experts and has now been patched in Docker version 29.3.1.
How Attackers Can Exploit This Flaw and Its Impact
The root of the issue lies in how the Docker daemon processes oversized HTTP requests. Attackers can pad container creation requests with large payloads—above 1MB—causing the request to be dropped without proper authorization checks. This mechanism tricks Docker into creating containers with root access to the host. Consequently, attackers could gain access to critical information like cloud credentials, SSH keys, and Kubernetes configurations. Moreover, AI-powered agents inside Docker environments could be manipulated to execute malicious commands by embedding carefully crafted request padding. This level of access opens the door for a wide range of malicious activities, including taking control of cloud accounts and servers. Experts advise that, until patched, users should avoid authorization plugins that rely solely on request body inspection. Instead, they recommend limitingDocker API access and operating in rootless mode when possible, to minimize risks.
Expand Your Tech Knowledge
Stay informed on the revolutionary breakthroughs in Quantum Computing research.
Stay inspired by the vast knowledge available on Wikipedia.
DataProtection-V1